Security researcher Rafay Baloch has identified vulnerabilities in the websites of Microsoft and Twilio. He has also discovered a number of flaws in the ProActive content management system (CMS).
Twilio rushed to address the Cross-site request forgery (CSRF) vulnerability identified by the expert.
To demonstrate his findings, Baloch published a proof-of-concept video on his personal blog in which he shows how tools such as Burp Suite and Tamper Data can be utilized to identify such security holes.
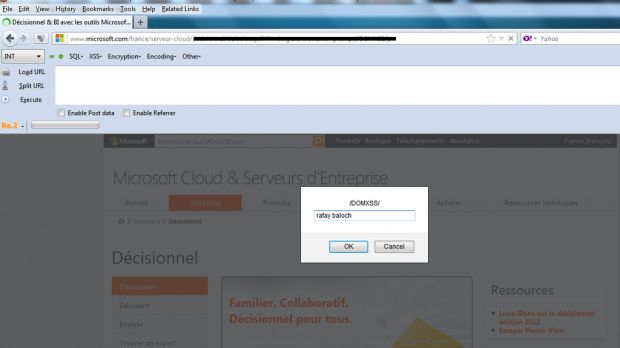
Microsoft also rushed to fix the DOM-based cross-site scripting vulnerability discovered by the researcher on the Microsoft Cloud and Server site dedicated to users from France.
“When exploiting a DOM based XSS vulnerability, we are usually targeting client side JavaScript. The vulnerability occurs due to use of dangerous sinks and sources,” Baloch told Softpedia.
“The vulnerability primarily occurs when the input passed through the client side JavaScript is not filtered before rendering it to the page.”
The researcher says that another similar vulnerability is currently being validated by Microsoft.
Unfortunately, CMS ProActive hasn’t taken any steps to address the issues reported by the expert.
“I found three different vulnerabilities inside ProActive CMS. It has not been updated for a while, it's really unsecure. I did not find a single CSRF token in its forms,” he explained.
“Next, I found a stored XSS inside the new user field. The input was not being properly validated / checked. Along with it, I also found an open redirection vulnerability which could be exploited by an attacker to carry out phishing attacks.”
In December 2012, Rafay Baloch identified a remote code execution vulnerability on PayPal.com. At the time, the company rewarded him with $10,000 (7,500 EUR) for his work.
Screenshots of other vulnerabilities identified by the expert can be found on this slide.

 14 DAY TRIAL //
14 DAY TRIAL //