Law enforcement authorities in Europe have raided tens or possibly even hundreds of individuals suspected of using the BlackShades remote access Trojan (RAT).
According to French publication RTL, over 70 locations were searched on Tuesday in France, including in Paris, Lille and Bordeaux.
On a hacker forum, one user from Germany reported being visited by German police because he had purchased the BlackShades RAT. Agents seized a PC, a laptop, an external hard drive, and cryptography-related documents.
One individual from the Netherlands also claimed to have been visited by seven agents of the country’s cybercrime police. He said that his phone, computer and other electronics were seized.
Nu.nl has reached out to Dutch authorities to get confirmation, but the police say that it’s an ongoing investigation, so they can’t make any statements.
Hacker forum members have also reported raids in Belgium, the UK, Denmark, Italy, Sweden and even Australia. However, we haven’t been able to confirm these reports.
In the summer of 2012, following a 2-year investigation, the FBI announced the arrests of 23 alleged cybercriminals. One of them was then 21-year-old Michael Hogue, aka xVisceral, believed to be one of the creators of BlackShades.
xVisceral announced his retirement from the hacking scene in August 2011. However, he remained active on several cybercrime forums, even offering support for BlackShades customers.
L’Express reports that after xVisceral’s arrest, French police were provided with a list of local BlackShades customers. It’s possible that authorities in other countries have been provided with such information as well.
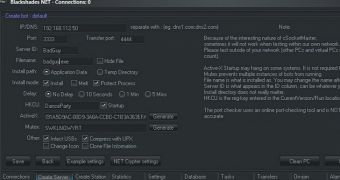
BlackShades is a RAT that can be used to take over an infected computer, including for monitoring webcams, logging keystrokes and stealing files. It’s currently being sold for between $40 (€30) and $100 (€73) on cybercrime forums.
At the time when Hogue was arrested, security experts warned that other members of the cybercriminal group would likely continue working on improving and distributing the RAT, and they were right.
In late November 2013, Symantec warned of an increase in the usage of BlackShades. At the time, researchers revealed that cybercriminals were using the Cool Exploit Kit to distribute the threat. Cool EK became the most prevalent exploit kit after the arrest of the author of BlackHole exploit kit.
We’ll probably find out more about this operation once authorities come forward with a statement to the press. If there have been so many raids in Europe, Europol’s EC3 has been most likely involved, so we should expect to hear from them.
Update. MalwareTech reports that the FBI is coordinating the operation.
Update 2. Rickey Gevers of Digital Investigation also shares some information regarding the FBI's involvement.
 14 DAY TRIAL //
14 DAY TRIAL //