Last week, the Joomla CMS team released an urgent patch for its project that fixed a critical SQL injection vulnerability that easily handed over control of the site to any attacker knowing what to look for.
The SQL injection flaw (CVE-2015-7297, CVE-2015-7857, CVE-2015-7858) was discovered by Trustwave researchers, and was announced in separate blog posts on the Joomla and Trustwave sites.
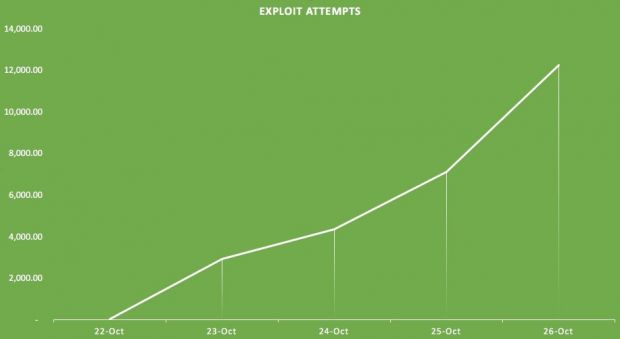
According to reports coming out of Sucuri, a vendor of cyber-security products for websites (WordPress, Joomla, Magento, etc.), only four hours after details of the vulnerability had been published, first attacks were recorded on the first site, with more attacks coming the following days, gradually growing across time, and currently reaching over 12,000 exploit attempts per day.
Fortunately for the first attacked site, its webmaster, who at that point was off duty, had deployed Sucuri WAF (Web Application Firewall), which had already been updated to detect and prevent that particular type of attack.
Subsequent attacks grew in sophistication, with attackers working on their exploit code so it would be able to detect and avoid older versions of Joomla, and only target the latest 3.x branch, which is affected by this issue.
"This data tell us is that the average webmaster has less than 24 hours to patch a site after a serious disclosure like this," says Daniel Cid, Founder and CTO at Sucuri. "That’s for the average site (small to medium size). If you have a popular site, you have a couple of hours only, from disclosure to attack and you have to react fast."

 14 DAY TRIAL //
14 DAY TRIAL //