A man or group using the moniker The Shadow Brokers claims to have hacked a covert and sophisticated cyber-espionage group that various security vendors have unofficially linked with the NSA in the past, called the Equation Group (or just Equation).
The Shadow Brokers made their presence felt online on Saturday, August 13, when they tweeted a link to a GitHub repository where they hosted instructions for an online auction, along with cyber-weapons that supposedly belonged to the Equation Group.
The GitHub repo has been taken down in the meantime, but you can access a cached version here or check out this screenshot we took of the page.
The Shadow Brokers are holding an auction for NSA's hacking tools
In the GitHub repo, before it was taken down, there were two encrypted archives, containing the tools stolen from the Equation Group.
The Shadow Brokers included the password for only one archive, which they offered for free, as a teaser and sign of good faith. The other archive contained the rest of the files, for which only the auction winner would receive the password via email.
The auction process is simple. Bidders must send money to a Bitcoin wallet. Bitcoin transactions support a metadata field that allows users to enter custom text. Bidders must enter their email address in this field, as a way for the hackers to reach them.
Hackers hope to make over 1 million Bitcoin ($568 million)
The person with the highest bid wins. Only one person wins. People who placed bids won't receive their money back. The Shadow Brokers say that if they gather more than 1 million Bitcoin ($568 million), they will release more files for free from the Equation Group trove, as a thank you.
The GitHub repo has been deleted, but The Shadow Brokers have posted the same instructions on their Tumblr account and in PasteBin pages. Below are the most important sections from their original instructions. English grammar and spelling left as they were:
“ We auction best files to highest bidder. Auction files better than stuxnet. Auction files better than free files we already give you. The party which sends most bitcoins to address: [REDACTED by Softpedia] before bidding stops is winner, we tell how to decrypt. Very important!!! When you send bitcoin you add additional output to transaction. You add OP_Return output. In Op_Return output you put your (bidder) contact info. We suggest use bitmessage or I2P-bote email address. No other information will be disclosed by us publicly. Do not believe unsigned messages. We will contact winner with decryption instructions. Winner can do with files as they please, we not release files to public. ”
“ Q: Why I want auction files, why send bitcoin? A: If you like free files (proof), you send bitcoin. If you want know your networks hacked, you send bitcoin. If you want hack networks as like equation group, you send bitcoin. If you want reverse, write many words, make big name for self, get many customers, you send bitcoin. If want to know what we take, you send bitcoin. ”
“ Q: What is in auction files? A: Is secret. Equation Group not know what lost. We want Equation Group to bid so we keep secret. You bid against Equation Group, win and find out or bid pump price up, piss them off, everyone wins. ”
“ Q: What if bid and no win, get bitcoins back? A: Sorry lose bidding war lose bitcoin and files. Lose Lose. Bid to win! But maybe not total loss. Instead to losers we give consolation prize. If our auction raises 1,000,000 (million) btc total, then we dump more Equation Group files, same quality, unencrypted, for free, to everyone. ”
“ Q: When does auction end? A: Unknown. When we feel is time to end. Keep bidding until we announce winner. ”
“ Q: Why I trust you? A: No trust, risk. You like reward, you take risk, maybe win, maybe not, no guarantees. There could be hack, steal, jail, dead, or war tomorrow. You worry more, protect self from other bidders, trolls, and haters. ”
As you can see from their texts, The Shadow Brokers are light on details but heavy on expectations.Auction files look authentic at a quick glance
According to an analysis from Risk Based Security (RBS), the files and folders included in the free package are dated to as back as 2010 (directories) and 2013 (files).
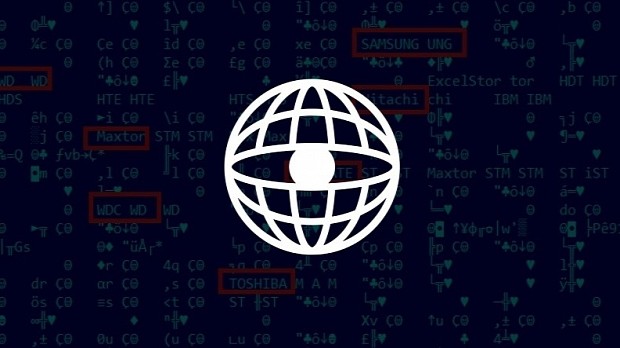
The free files mostly contain exploits for hacking enterprise firewalls such as Fortinet's Fortigate, various Cisco products (PIX, ASA), the TOPSEC firewall, and others.
A full list of exploits included in the free sample is available here while a gallery can be accessed at the end of this article. Exploit codenames include terms such as BARGLEE, BANANAGLEE, BLASTSTING, EPICBANANA, BUZZDIRECTION, and others. All exploit names were publicly known since 2013, when a German newspaper published a leaked NSA cyberweapons catalog.
The free file archive was compiled on July 26, 2016, while most of the social media accounts The Shadow Brokers use were registered on August 1, 2016, and afterward.
There are doubts about the legitimacy of the hackers' claims
It is highly unlikely that the hackers compromised NSA/Equation servers. The more believable scenario is that they hacked one of the live servers where the Equation Group deployed these tools for a live operation and stole them from there.
At this point, this is either the most elaborate scam ever attempted, or the Equation Group managed to have more pathetic security measures than the Hacking Team, a cyber-surveillance firm that got hacked in June 2016 and had all its hacking tools dumped online.
At the time of writing, the highest bid in the Bitcoin wallet address is for 0.03733067 Bitcoin ($21.2), which is not even close to the sum The Shadow Brokers expected to receive.
Below are some tweets from infosec industry experts to put some things into perspective.
9) This leak is likely a warning that someone can prove US responsibility for any attacks that originated from this malware server. — Edward Snowden (@Snowden) August 16, 2016
This dump does not support the assertion that NSA was hacked. That sort of access is too valuable to waste for (almost) any reason. — the grugq (@thegrugq) August 15, 2016
I would guess: the dump is the take from a counter hack against a pivot/C2 that was mistakenly loaded with too much data. Shit happens. — the grugq (@thegrugq) August 15, 2016
Presenting wild speculation as facts on Twitter should be an Olympic sport. #EquationGroup — Dan Rosenberg (@djrbliss) August 15, 2016
To me it looks like someone got control over a C2 server that contained NSA TAO tools. #EquationGroup #ShadowBrokers — Rickey Gevers (@UID_) August 15, 2016
Maybe APT28 is low on $$$ since they are raising operational funds via a auction of #EquationGroup 's toolset. Why not a bakesale instead? — Ben Heise (@benheise) August 15, 2016
Which means either: 1. This is fake 2. Avast is wrong or 3. EG is still using 10-year old patched vulnerabilities to hack around networks. — Pwn All The Things (@pwnallthethings) August 15, 2016
Assuming this is legit and NSA, this raises some interesting challenges for the Vulnerabilities Equities Process inside IC. — Pwn All The Things (@pwnallthethings) August 15, 2016
@botherder there are nothing from Equation, only names from ANT catalog — codelancer (@codelancer) August 15, 2016
If at all legit, this #EquationGroup leak might be a compromise of a LP. It doesn't seem to contain source code of actual implants. — Nex ~ Claudio (@botherder) August 15, 2016
This #EquationGroup free dump seems mostly binary builds, installation scripts, and general configuration for a C&C. Seems credible. — Nex ~ Claudio (@botherder) August 15, 2016
Well thanks to the #equationgroup hack now you know which routers and firewalls to buy — Alex Ionescu (@aionescu) August 15, 2016

 14 DAY TRIAL //
14 DAY TRIAL //