The Intercept has published today new Snowden documents that reveal an official connection between official NSA cyber-weapons and the malware dumped by The Shadow Brokers.
The documents are internal NSA operations manuals that describe how CNE (Computer Network Exploitation) tools must be used.
The documents that The Intercept received from Snowden a few years back but never published describe a hacking system called BADDECISION.
Leaked exploit was part of a bigger hacking system
The BADDECISION system is made up of the FOXACID server, the SECONDDATE exploit, and the BLINDDATE field operations software, among other things.
The SECONDDATE exploit is a tool that works at the network level by intercepting web requests and redirecting them to the FOXACID server, where the user is infected with the desired malware.
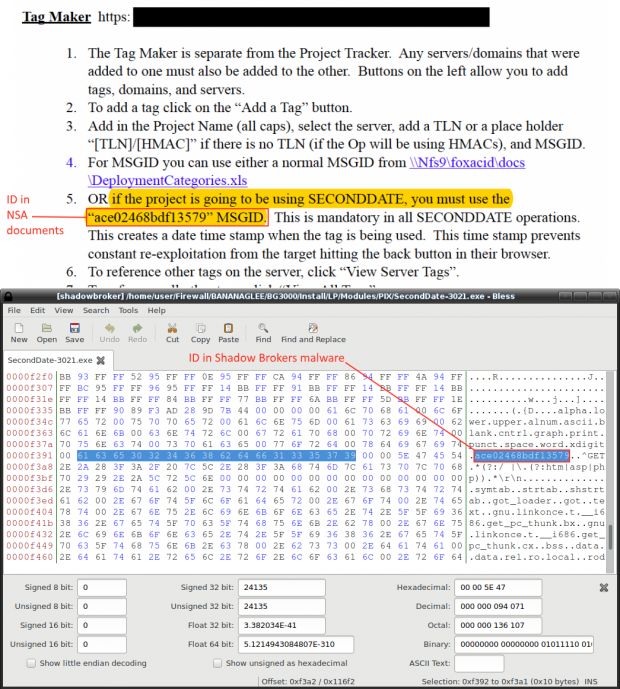
According to procedures described in the operations manual (page 28), NSA employees must use IDs to tag victims sent to the FOXACID server via different exploits. The document reveals that SECONDDATE's ID is ace02468bdf13579.
This very same ID was found in 14 different files in the files named SECONDDATE included in the Shadow Brokers leak.
NSA used exploit in Pakistan and Lebanon
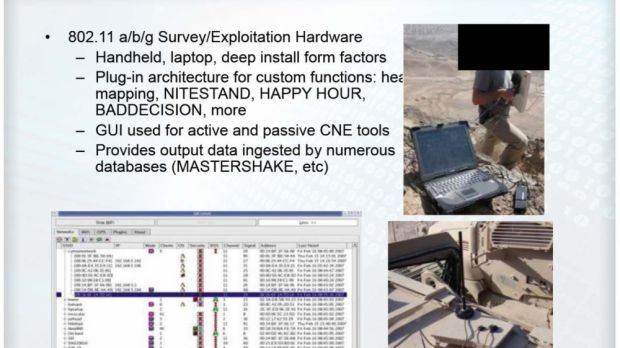
Furthermore, other documents revealed that the NSA used a system called BLINDDATE to automate SECONDDATE attacks on Wi-Fi networks in the field.
BLINDDATE is a hardware system running custom software that can launch MitM (man-in-the-middle) attacks leveraging SECONDDATE, HAPPY HOUR, NITESTAND, and others.
The equipment is used in the field, in the range of an enemy's wireless network. BLINDDATE is a laptop with a giant antenna, which can also be mounted on drones, and redirect a Wi-Fi network's web traffic to the NSA FOXACID server.
According to Snowden documents leaked in 2013, BLINDDATE was used to spy on Pakistan's National Telecommunications Corporation’s (NTC) VIP Division and Lebanon's major ISPs. These campaigns provided the NSA with information on Pakistan’s Green Line communications network, its civilian and military leadership, and on Hizballah's Unit 1800 activities.
Before The Intercept made the connection between the Shadow Brokers leak with actual NSA cyber-weapons, Kaspersky researchers tied the malware in the group's data dump to tools used by the Equation Group cyber-espionage APT, believed to be linked to the NSA.
 14 DAY TRIAL //
14 DAY TRIAL //