TMZ, everybody's favorite gossip site, was compromised by malicious advertisers that managed to infect some of the site's advertising spots with ads that contained malicious JavaScript code, thus redirecting users to more dangerous threats.
Malwarebytes, who discovered this issue, says this campaign is part of the same attack launched a few days back against other high-profile sites like Rotten Tomatoes and The Jerusalem Post, an Israeli online newspaper.
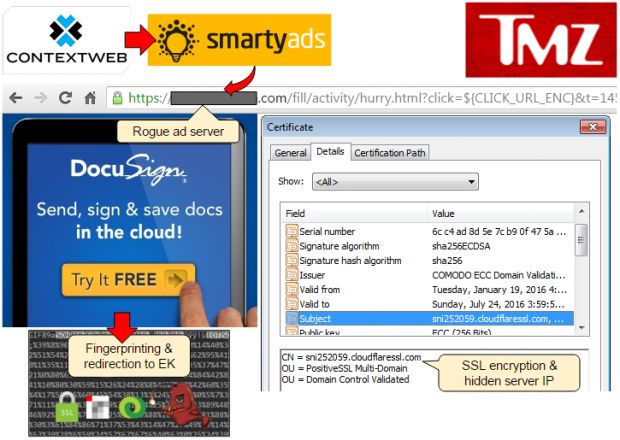
As before, the ads were delivered through the SmartyAds advertising platform.
"We’ve found out that most of the rogue advertisers are leveraging the CloudFlare infrastructure to hide their backend server and encrypt their traffic as well, along with using anonymous proxy registration details for the domain," explained Jérôme Segura from Malwarebytes last week, when the malverts were found on the Rotten Tomatoes site.
Despite the security vendor unmasking their activities, the malvertisers weren't deterred and simply created new fake profiles through which to deliver new malicious ads, via the same infrastructure they had before.
Malvertising was redirecting users to the Angler EK
TMZ traffic is usually at 30 million users per month, but only a fraction of these were exposed.
Mr. Segura said that the malvertising campaign was redirecting TMZ visitors through different Web servers, which were selecting only users with vulnerable browsers and operating systems, and sending them to a page that was hosting the Angler Exploit Kit.
Here, specially crafted malicious code would scan the user's computer for vulnerabilities and exploit them to deliver malware to all TMZ users.
Taking into account that TMZ charges around $0.19 per 1,000 ad impressions, this campaign was quite cheap to carry out. Additionally, malvertising also has a higher success rate than classic spam campaigns, doesn't rely only on social engineering tricks, and works silently without any signs of its presence, so we may see more of it in the future.

 14 DAY TRIAL //
14 DAY TRIAL //