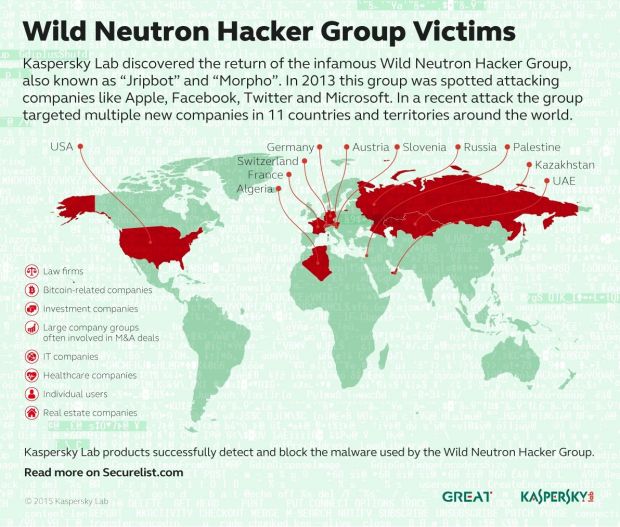
Kaspersky and Symantec are reporting on the return of the infamous Morpho hacker group, also known as Wild Neutron by some, a group that specifically targets big companies, for monetary gains.
First detected in 2011, the group's claim to fame comes from a series of attacks in 2013, when they managed to hit Twitter, Facebook, Apple, and Microsoft in a short period of time, back then using a Java zero-day exploit.
Morpho seems to be an international hacking group, focused on their own monetary gains
After laying low for a small period of time, new attacks are being reported by both Kaspersky and Symantec, and as before, they are targeting corporate entities.
"The attackers appear to be motivated by financial gain, either by using the information themselves for their own benefit or selling it to a third party," says Symantec.
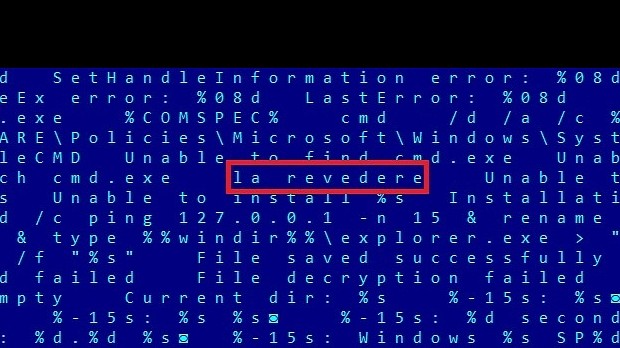
"The focus of these attacks suggests this is not a nation-state sponsored actor," adds Kaspersky, which then also goes to detail how it identified English, Russian, and Romanian words inside the analyzed malware.
The grouped switched from a Java exploit to an unknown Flash Player vulnerability
On a technical level, these new attacks seem to be using a combination between an unknown Flash Player exploit and a stolen Acer code signing certificate.
These allow attackers to take gain access to infected machines, and then either harvest sensitive data or take control of various services of the infected workstations.
To retrieve the data, Morpho used custom OpenSSH tunnel backdoors, protected using a hardcoded RSA private key.
These new series of attacks were detected in 2014 and 2015, and targeted IT, real estate, and investment companies in the US, France, Germany, Switzerland, Russian, Austria, United Arab Emirates, Slovenia, and Kazakhstan, as reported by Kaspersky. Symantec also reported attacks on Canadian companies.
 14 DAY TRIAL //
14 DAY TRIAL //