Speaking at the Black Hat Asia 2016 security conference in Singapore, two US researchers have explained how well-known Firefox extensions can be used by other (malicious) extensions to carry out attacks against users, The Register reports.
Last week, Boston University Ph.D. Ahmet Buyukkayhan and Northeastern University Professor William Robertson, presented their research in front of the Black Hat Asia attendees, revealing how holes in Mozilla's add-on ecosystem can be leveraged by attackers.
Extension reuse attack hides in plain sight
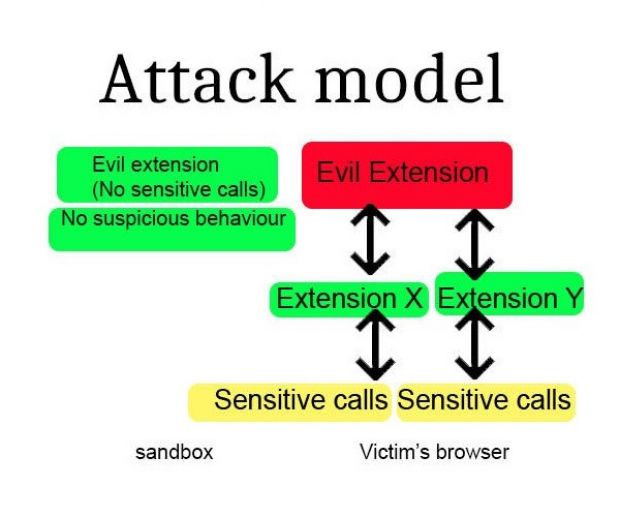
For the past two years, the two researchers have been creating malicious extensions which use a so-called "extension reuse" mechanism to make malicious calls to other extensions, which then pass them along to the underlying system.
Since all calls made by an extension through Firefox are executed with elevated privileges, attackers have a broad spectrum of attack possibilities at their disposal.
Even worse, one of these malicious extensions can easily go through Mozilla's review process which all extensions must go through to be added to their add-on portal.
Attack is undetectable to Mozilla's add-on reviewers
Since the malicious extension doesn't make any dangerous calls to Firefox's most sensitive inner parts, automated and human reviewers can't pick up the malicious behavior.
Through this attack scenario, researchers managed to exploit popular Firefox add-ons to carry out malicious actions. In their tests, they used add-ons such as the highly-popular GreaseMonkey add-on (1.5 million active installs), Video DownloadHelper (6.5 million active installs), and NoScript (2.5 million active installs).
They even carried out a live experiment, submitting a harmless add-on to Mozilla that leverages the extension reuse attack scenario, even requesting a full review from Mozilla's staff.
To make things easier, their test extension, called ValidateThisWebsite, contained only 50 lines of code and was left unobfuscated for easy access to its source code. Mozilla reviewers approved the extension without any red flags.
The two researchers ended up revealing the attack to Mozilla' staff and even provided them with the source code of the Crossfire framework that will help reviewers in identifying these types of attacks.
UPDATE 1: Mozilla has provided the following statement on the "extension reuse" attack scenario.
"The way add-ons are implemented in Firefox today allows for the scenario hypothesized and presented at Black Hat Asia. The method described relies on a popular add-on that is vulnerable to be installed, and then for the add-on that takes advantage of that vulnerability to also be installed," says Nick Nguyen, VP of Product for Firefox.
"Because risks such as this one exist, we are evolving both our core product and our extensions platform to build in greater security. The new set of browser extension APIs that make up WebExtensions, which are available in Firefox today, are inherently more secure than traditional add-ons, and are not vulnerable to the particular attack outlined in the presentation at Black Hat Asia. As part of our electrolysis initiative - our project to introduce multi-process architecture to Firefox later this year - we will start to sandbox Firefox extensions so that they cannot share code. "
UPDATE 2: The research paper detailing the attack is available here.
UPDATE 3: NoScript's author also provided his opinions on this matter.

 14 DAY TRIAL //
14 DAY TRIAL //