The Windows Troubleshooting Platform (WTP) has joined a select list of legitimate Windows services abused to install malware on users' computers.
According to Proofpoint researchers, this latest trick was used inside Word documents spread via a recent spam campaign.
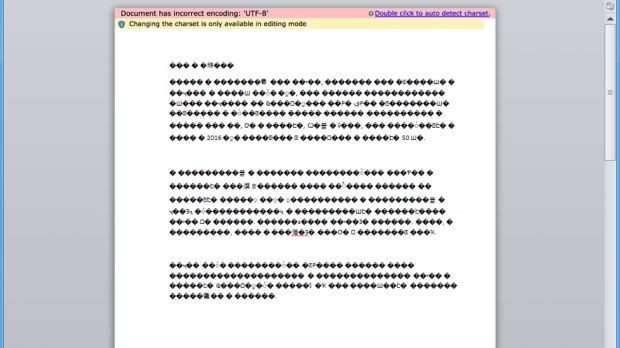
When users would open this Word document, they'd be greeted by a jumble of random characters and a warning at the top of the document. This warning reads "Document has incorrect encoding: 'UTF-8' Double click to auto detect charset."
The warning is nothing more than an OLE object, an interactive item that can be embedded anywhere inside Office documents.
Most users are conditioned to click through troubleshooting windows
Proofpoint researchers say that double-clicking this alert will launch a DIAGCAB file into execution.
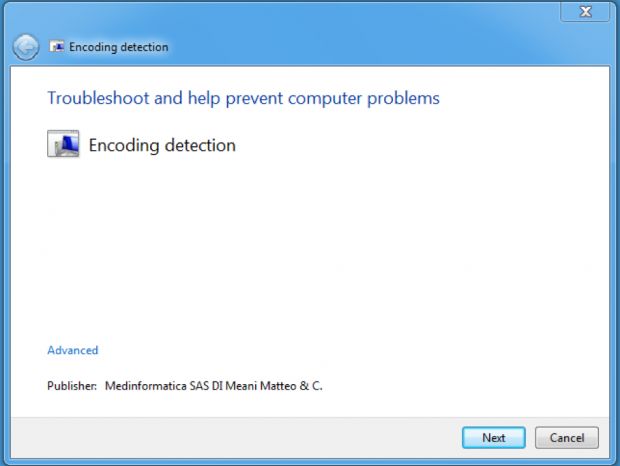
DIAGCAB is a file format attached to the Windows Troubleshooting Platform, a system Microsoft created to allow software vendors and OEMs to automate the execution of various troubleshooting and auto-repair operations.
All users have seen and clicked through troubleshooting windows when they have problems connecting to the Internet and select the "Troubleshoot connection" option. Sometimes this process repairs their network settings, so most users are conditioned to click "Next" whenever they see troubleshooting windows.
Launching PowerShell scripts via DIAGCAB files
In the case of this recent spam campaign, double-clicking the warning to detect the document's character set launches a troubleshooting window, which is nothing more than a DIAGCAB file. This file contains a series of automated PowerShell scripts which, according to Proofpoint, download and install the LatentBot backdoor trojan.
Technically, there is no difference between macro scripts and these troubleshooting scripts, since both allow an attacker to execute a series of automated operations on the victim's computer.
The difference is that security software installed on the user's PC is programmed to watch for malware that might get installed via Office macro scripts, while troubleshooting packages are ignored in totality.
Besides the Windows Troubleshooting Platform (WTP), in the past, malware authors also abused other Windows services and features such as the Windows Management Instrumentation (WMI), Office Interoperability, Background Intelligent Transfer Service, and the Task Scheduler.
Fortunately, his new trick requires user interaction, just like macro scripts, so users who went through security training will most likely spot the dodgy warning message and call in their sysadmin for further investigation.

 14 DAY TRIAL //
14 DAY TRIAL //