Microsoft has recently released its June 2012 security update and with it the company also released an advisory to warn customers of a serious zero-day exploit that affects Internet Explorer. While there isn’t a permanent patch for this issue, the Redmond company has made available a “Fix it” solution.
In order to exploit the flaw, an attacker has to host a website that contains a malicious webpage. The cybercriminal would have to social engineer the victim to convince him/her to visit the domain.
If exploited successfully, the vulnerability would allow the attacker to gain the same rights as the customer who is logged in at the time.
ZDNet reports that the existence of this security hole and the fact that it’s actively exploited may have been the factors that determined Google to introduce the “state-sponsored attack” warnings. We believe this to be true based on the advisory that the search engine giant has released on its security blog.
Some users might be aware of the fact that one of Microsoft’s security bulletins, MS12-037, has addressed a similar issue in Internet Explorer, but that’s not the same as the vulnerability that remained unpatched.
According to experts from McAfee, this particular attack is also active in the wild and exploits a use-after-free weakness. A detailed analysis of the flaw has revealed that it works on all major Windows platforms, including Vista and 7.
“It leverages return-oriented programming (ROP) exploitation technology to bypass with data execution (DEP) and address space layout randomization (ASLR) protections, and hook-hopping evasion techniques to evade host-based IPS detections,” McAfee’s Yichong Lin explained.
“It requires the victim’s system to run an old Java virtual machine that came with a non-ASLR version of msvcr71.dll. If Java is not installed or there is no non-ASLR version of msvcr71.dll in the system, the exploit won’t work, although it will cause IE to crash.”
To patch this Internet Explorer vulnerability users are advised to install the latest updates.
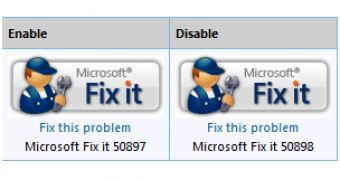
For the unpatched flaw the company has released the 2719615 security advisory, along with the Fix It solution that’s available here.
Update. We want to clarify that the first vulnerability we described is actually in Microsoft XML Core Services, Internet Explorer being used as the attack vector.
“Microsoft released a Fix it in Security Advisory 2719615 as a safe, easily applied workaround to help protect customers from attackers attempting to exploit the MSXML issue through Internet Explorer,” said Yunsun Wee, director at Microsoft Trustworthy Computing
“The vulnerability does not reside in IE but because the browser may be used as an attack vector, Microsoft encourages customers to apply the workaround to their browsers until we release a security update.”
 14 DAY TRIAL //
14 DAY TRIAL //