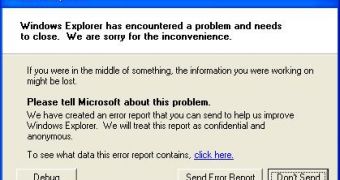
A recent report published by German media revealed that the NSA secretly intercepted Windows error reports in order to find out the latest vulnerabilities in the operating system and exploit them in order to wiretap a number of computers.
It turns out that doing this is not at all difficult, as the information submitted through the Dr. Watson service is not encrypted and delivered to Microsoft’s servers via a regular HTTP connection.
Security vendor Websense has discovered that whenever a user connects a USB device to a Windows computer, an automatic report comprising information about the machine and the USB device itself is being sent to Microsoft.
This information includes date, USB device manufacturer, device identifier, revision, host computer OS, service pack and update version, manufacturer, model and name, BIOS version, default language and unique machine identifier.
“While this information is no doubt critical for Microsoft to debug application crashes and hardware configurations, it can represent a significant information leak when it leaves an organization without being encrypted,” Websense explained.
According to the report, Windows XP, Vista, and Windows 7 are all affected by this, but Websense explains that application crash reports developed by Microsoft for OS X computers comprise the same vulnerability.
“Our research indicates that by default many organizations are reporting (in clear-text) specific information about applications, services, and hardware through Microsoft Error Reporting. These application reports are not just limited to crashes, but also events such as failed application updates, USB device insertions, and in some cases even TCP Timeouts between computers on the network, a large percentage of which is sent in HTTP clear text.”
In the end, Websense recommends organizations to put in place group policies to enforce encryption until Microsoft updates its bug reporting system to protect user data.
“We recommend services that report application telemetry and contain information about the security environment and underlying network infrastructure should be encrypted with SSL at a minimum, ideally using TLS 1.2. Applications that report this information without encrypting data risk leaking information at multiple points.”
 14 DAY TRIAL //
14 DAY TRIAL //