Users will be in full control of their PCs and will be able to install any operating system they want, Microsoft stressed, ending the controversy over the possibility that Windows 8 machines with UEFI Secure Boot could lock out third-party platforms. Not the case, the software giant says.
Tony Mangefeste, from Microsoft’s Ecosystem team set the record straight in a post on the ‘Building Windows 8’ blog, noting that customers will have the possibility of disabling UEFI secure boot, to install even older operating systems, including Linux, on their PC.
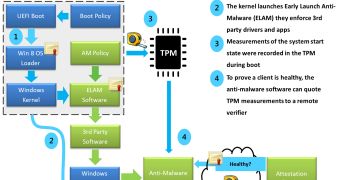
Windows 8, in combination with UEFI 2.3.1 addresses a security hole in the current design of BIOS which lets any loader, including for malicious code such as rootkits, start ahead of the operating system.
In contrast to BIOS, the Unified Extensible Firmware Interface will only allow verified OS loaders to start, as long as UEFI secure boot is enabled. This means that malware can no longer switch the boot loader.
“For Windows customers, Microsoft is using the Windows Certification program to ensure that systems shipping with Windows 8 have secure boot enabled by default, that firmware not allow programmatic control of secure boot (to prevent malware from disabling security policies in firmware), and that OEMs prevent unauthorized attempts at updating firmware that could compromise system integrity,” Mangefeste explained.
What this means is that while a rootkit or any other piece of malware using a boot loader won’t be able to run during startup on a Windows 8 machine with Windows 8 PCs with UEFI Secure Boot, customers would still have the option of disabling the security mitigation and run other legitimate software, including non-Windows operating system loaders.
Mangefeste provided some highlights about what protecting the pre-OS environment with UEFI means for Windows 8 customers:
“• UEFI allows firmware to implement a security policy
• Secure boot is a UEFI protocol not a Windows 8 feature
• UEFI secure boot is part of Windows 8 secured boot architecture
• Windows 8 utilizes secure boot to ensure that the pre-OS environment is secure
• Secure boot doesn’t “lock out” operating system loaders, but is is a policy that allows firmware to validate authenticity of components
• OEMs have the ability to customize their firmware to meet the needs of their customers by customizing the level of certificate and policy management on their platform
• Microsoft does not mandate or control the settings on PC firmware that control or enable secured boot from any operating system other than Windows.”
 14 DAY TRIAL //
14 DAY TRIAL //