The controversial UGNazi group claims to have gained access to Google’s Mark Monitor account by social engineering an employee into associating one of the hackers’ email address with google.com.
“So, Today, we are releasing our statement on that no one on the Internet is safe from UGNazi. On June 11th we gained access to Google's MarkMonitor account,” the hackers wrote on Pastebin.
“Our email address [email protected] was successfully updated on Google's Mark-Monitor Account. The agent that helped us reset the account should get some what of credit, she helped us alot on reseting Google's MarkMonitor account :)”
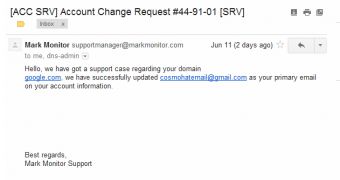
They also published an image that allegedly represents the confirmation email sent by Mark Monitor’s support team.
“P.S Google, I suggest you move to a more secure registrar. but then again, we are Social Engineering Gods. So, this just goes to show, even Google can be Social Engineered,” they said.
Cosmo, the hacker that took credit for the social engineering part, has revealed that the person he convinced to reset the account is Olga Bougri, client services manager at Mark Monitor.
Mark Monitor is a company that provides Internet brand protection services and specializes in software products for domain management, anti-fraud, anti-piracy and brand protection. According to Wikipedia, Google is listed as one of its Fortune 100 customers.
We have been unable to determine the dangers posed to Google by a potential breach to the organization’s account, but the hackers claim that they could have caused serious damage.
However, they also state that Mark Monitor has addressed the issue and they no longer have access to the account.
Over 24 hours have passed since we contacted Mark Monitor representatives seeking comment on the hackers’ claims, but at press time we haven’t received a response. We’ll update this post as soon as new information becomes available.
If the hackers’ claims turn out to be true, it wouldn’t be the first time when UGNazi uses social engineering to gain access to a company’s systems. A short while ago they leveraged the same technique to breach CloudFlare, possibly via AT&T.
Update. Mark Monitor representatives have responded to our inquiry. They deny being breached by UGNazi. As expected, it's not an easy task to gain access to such a high-profile account.
"These reports are completely false. We protect the domain name portfolios of the most highly trafficked sites so we take security very seriously. However, we cannot control what people claim," said a company representative.
Update2. Mark Monitor has also confirmed that the image made public by the hackers is a fake.
"That is not an email that we sent to a customer or to anyone else, for that matter."
 14 DAY TRIAL //
14 DAY TRIAL //