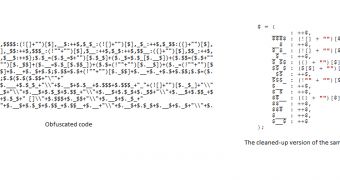
Experts from security firm Avast! have identified some suspicious-looking pieces of code on a number of Joomla websites. Upon a closer analysis, researchers have found that the obfuscated code (see screenshot) could actually be utilized to spread malware.
The first thing the experts have noticed was that the code was placed between (<script>) HTML tags, which indicates the presence of JavaScript.
Interestingly, the tags were placed so that users who analyzed the file in question would not be able to see them except if they had word wrap enabled or if they had scrolled horizontally.
The code itself is cleverly obfuscated because it doesn’t contain any letter or numbers, only a bunch of $ signs and some mathematical symbols.
However, a closer look at it shows that it actually hides a script.
For instance, the first characters read “$=~[];”. The square Brackets ([]) actually represent a zero. The tilde sign in front of it actually negates it bitwise, turning it into -1.
So, “$=~[];” actually means that -1 is stored in the $ variable, and the same type of logic applies to the rest of the code.
When it’s executed, the payload checks if the victim uses the Chrome web browser and shuffles all link referrers from the webpage, so that when the internaut clicks on one link, he/she is taken to another page than the one they desired.
Another piece of code identified on the infected pages ensures that when either one of the links is clicked, the user is taken to a website which helps the scammers make money each time someone visits it.
In addition, the cybercriminals have added a piece of code (also hidden from plain sight) which tells search engines where to find the original version of the page, the clean one.
“This means if a search engine robot visits an infected page, it is told that the original version is somewhere else, and indexes only this original version. If you search for any keywords on your page, the search engine will instead present results of the ‘canonical’ version. In other words, an infected page will not be shown in search engine results,” experts explained.
The complete analysis of the code and a deobfuscator developed by the experts is available on the Avast! Blog.
 14 DAY TRIAL //
14 DAY TRIAL //