The notorious Stuxnet worm has become a symbol of sophisticated cyberattacks ever since its 1.001 version was discovered in 2010. However, a new report published by Symantec shows that the development of the malware may have started much sooner than initially believed.
The security firm has uncovered Stuxnet 0.5, a version that’s been in development since as early as November 2005, and seen in the wild since as early as November 2007. It stopped spreading on July 4, 2009.
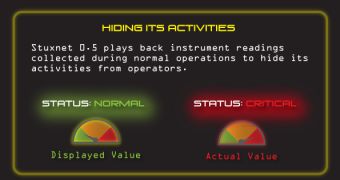
Stuxnet 0.5 wasn’t as aggressive as the later versions, but it was still capable of causing some serious damage.
While its main goal was to target Iranian nuclear facilities, this older variant contained an alternative attack strategy. It was designed to close valves within the uranium enrichment facility at Natanz, Iran.
“Whether Stuxnet 0.5 was successful is unclear, but later versions of Stuxnet were developed using a different development framework, became more aggressive, and employed a different attack strategy that changed the speeds of the centrifuges instead suggesting Stuxnet 0.5 did not completely fulfill the attacker’s goals,” Symantec explains in the repot.
Unlike later versions of Stuxnet, which were based on the Tilded platform, the 0.5 version was based on the Flamer platform.
Another noteworthy thing about Stuxnet 0.5 is that it had a working payload against Siemens 417 programmable logic controllers (PLCs), but it did not contain any Microsoft exploits.
Over the past year, Symantec has uncovered a small number of dormant infections in countries such as Iran (47%), the United States (21%), Italy (9%), Germany and Luxembourg.
The security solutions provider has found evidence which suggests that even older versions of Stuxnet exist, some of which have been in operations since as early as 2005.
The detailed report about Stuxnet 0.5 is available here.
Symantec has also published an interesting video which explains how Stuxnet 0.5 attempted to sabotage the Natanz facility:
 14 DAY TRIAL //
14 DAY TRIAL //