Security researchers at Italian firm ITSEC discovered that Windows 8 comes with a security flaw that could allow hackers to install malware on a vulnerable computer.
It’s all possible because of the Unified Extensible Firmware Interface (UEFI), an updated version of BIOS, which is available on Microsoft products since the debut of the 64-bit version of Windows 7.
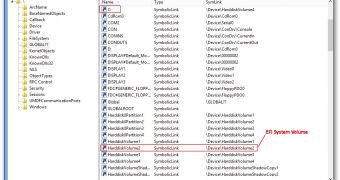
In just a few words, the security researchers managed to develop a separate UEFI bootloader that can be installed on the vulnerable computers in order to replace the standard Windows 8 UEFI bootloader.
“Our bootloader hooked the UEFI disk I/O routines and it intercepted the loading of the Windows 8 kernel, thus our bootkit tampered the kernel by disabling the security features used by Windows to prevent the loading of unsigned drivers,” Marco Giuliani, director of ITSEC, was quoted as saying by The Register.
What’s more, the same exploit could be used on some other platforms too, including OS X and Linux distributions, which is a bit worrying since both are getting more popular these days. OS X already uses UEFI since 2010 and the vulnerability can be exploited in a similar way.
Talking about Windows 8’s security level, Gerry Egan, Symantec senior director, product management, said that Microsoft doesn’t seem to spend too much time working on this chapter, emphasizing that a third-party security app will most likely be needed.
“It's partially true that Windows 8 is more secure,” Egan explained. “But underneath is a traditional Windows-Intel desktop, which is backward compatible with both the good code and the bad.”
The whole analysis made by ITSEC is included in a very detailed blog post that can be read here.
 14 DAY TRIAL //
14 DAY TRIAL //