Security expert Prakhar Prasad has identified a couple of vulnerabilities on websites owned by Adobe. Although he reported both issues as soon as they were discovered, the company failed to properly coordinate the fixing process.
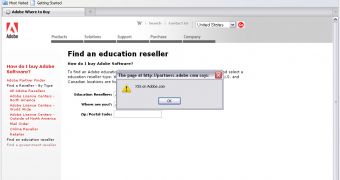
The first security hole is a cross-site scripting (XSS) vulnerability on the partners.adobe.com website.
The flaw was secretly fixed by the company, but if it had remained unpatched, it could have been leveraged by a cybercriminal to steal cookies or launch client-side exploits that could have allowed him to take full control of the victim’s device.
The bug has been reported to Adobe’s Product Security Incident Response Team on August 20, 2012, and although initially they seemed to be willing to collaborate with the researcher on addressing the issue, they failed to do so.
The second vulnerability is an open redirect found on the feeds.adobe.com site.
“The webpage takes a parameter 'nextPage' and redirects to it but while redirecting the page doesn't check whether the value in 'nextPage' parameter is white-listed or not, so ends up in an open redirect issue,” Prakhar explained on his blog.
To demonstrate his findings, the expert has published a proof-of-concept video.
“Although this type of vulnerability is not considered critical but it can 'hurt' an unsuspecting user when used in an attack like phishing or specifically spear-phishing where the user might be fooled to believe that the link belongs to Adobe Inc,” he said.
Security researcher Janne Ahlberg – who has focused many of his efforts on convincing organizations to instate proper vulnerability disclosure channels – claims that he is in a similar situation with Adobe. A bug he reported more than two months ago still remains unpatched.
Here is the video POC which demonstrates the existence of the open redirection vulnerability on the Adobe feeds site:
 14 DAY TRIAL //
14 DAY TRIAL // 