Security researcher Shadab Siddiqui identified a number of cross-site scripting (XSS) vulnerabilities in websites owned by the mobile phone manufacturer HTC, TATA-owned IT solution provider CMC Limited, IT firm Collabera, and Quick Heal, an Indian company that offers security products.
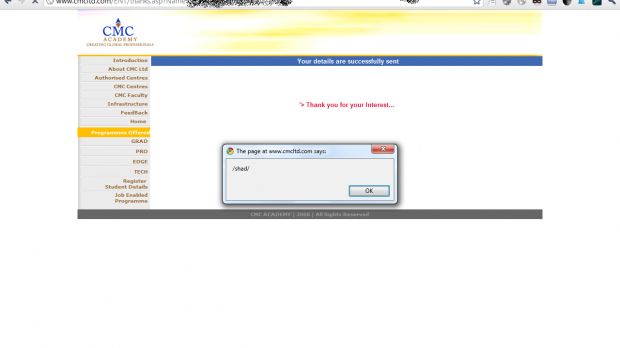
The screenshots provided by the researcher clearly demonstrate the existence of the security holes that can be easily leveraged to steal user cookies, launch phishing attacks and cause other types of damage to users.
The only thing with XSS vulnerabilities is that they require a certain level of user interaction when exploited, but as we’ve seen in numerous cases, that is not an impediment for skilled cybercriminals.
HTC and Quick Heal have been notified regarding the presence of these flaws around one month ago, CMC Limited and Collabera being informed at the end of March.
According to Siddiqui, he retested the sites and found that Collabera and Quick Heal addressed the issues, which shouldn’t come as a surprise, especially since they’re both companies that are active in the IT sector.
However, as in previous situations, we must note that it’s a shame some organizations fail to work together with security researchers to fix the flaws in their systems. Most experts we’ve seen are more than happy to collaborate with a firm that has a poorly coded and unsecured website.
Since he joined the Vulnerability Lab team, Shadab Siddiqui identified a number of security holes on the websites of high-profile vendors.
At the end of March, Apple fixed multiple Blind SQL Injection vulnerabilities that existed on its Education Seminars & Events site after the expert had reported the issues.
Another large company aided by Siddiqui and Vulnerability Lab's founder and CEO Benjamin Kunz Mejri was Oracle, whose public websites also presented Blind SQL Injection flaws.
Note. My Twitter account has been erroneously suspended. While this is sorted out, you can contact me via my author profile or follow me at @EduardKovacs1

 14 DAY TRIAL //
14 DAY TRIAL //