A long time has passed since its authors improved it, but experts found that the latest versions of the Xpiro family of file infectors came with a series of interesting capabilities.
According to Symantec researchers, the new Xpiro file infectors are persistent in nature. Secondly, they’re designed to infect both 32-bit and 64-bit executable files, particularly Intel 386 (32-bit), Intel 64 (64-bit) and AMD64 (64-bit) architectures.
Once it lands on a computer, Xpiro starts infecting win32 service files. Then, it looks for .lnk files on the victim’s desktop and in the start menu, and infects them.
The cybercriminals target link files because they’re aware these have the highest probability of being executed after a system reboot.
In the final phase, executable files from all fixed, removable and mapped drives are infected.
The malware’s main purpose is to steal information from the plagued device. This isn’t uncommon, but the fact that the new versions are much stealthier is certainly worth pointing out.
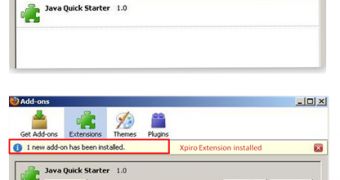
In addition, Xpiro has another trick up its sleeve. After it’s executed, the threat also adds its own extensions to Chrome and Firefox.
The extensions allow cybercriminals to perform various tasks. For example, the Firefox extension can be used to lower browser security, spy on the victim’s online activity, steal logs, and redirect internauts to arbitrary URLs.
The Firefox extension doesn’t show up in the extensions list. In Chrome, the malicious element has been named “Google Chrome 1.0” in an effort to avoid raising any suspicion.
Interestingly, Xpiro is also designed to prevent users from updating the browser. The web browser can’t update itself because the virus replaces the update URL with a local IP address.
“The Xpiro attackers have upgraded the threat’s functionality to be persistent, stealthier, and most importantly to cross-infect executable files on multiple platforms. Other infector families may be expected to follow suit and add sophisticated functionality to their arsenal in order to be more potent and viable across different platforms,” Symantec notes.
 14 DAY TRIAL //
14 DAY TRIAL //