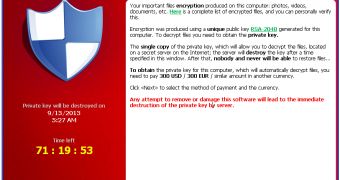
Security researchers from Emsisoft have come across a new ransomware family which they’ve dubbed CryptoLocker, or Trojan:Win32/Crilock. This particular piece of ransomware is designed to encrypt files on the infected device and keep them that way until a ransom is paid by the victim.
Interestingly, the files targeted by CryptoLocker are not ones that might be considered important by home users. Instead, the targeted files have extensions such as odt, doc, docx, xls, xlsx, ppt, pptx, mdb, accdb, rtf, mdf, dbf, psd, pdd, jpg, srf, sr2 ,bay ,crw, dcr, kdc, erf, mef, mrw, nef, nrw, raf, raw, rwl, rw2, ptx, pef, srw, x3f, der, cer, crt, pem, and p12.
This shows that the threat is designed to target businesses, to which the content of these files might be of great value.
According to experts, the ransomware is distributed via emails that inform recipients of customer complaints. The file that’s attached to these notifications is a downloader that’s designed to retrieve the actual malware.
Once it infects a device, CryptoLocker creates a registry entry to make sure it starts at every boot. Then, it establishes communications with its command and control (C&C) server. First, it attempts to contact a hardcoded IP address. If that fails, apparently random C&C domains are generated based on a domain generation algorithm.
After a C&C server is found, the malware starts communicating with it via traffic that’s encrypted using RSA encryption.
“Using RSA based encryption for the communication not only allows the attacker to obfuscate the actual conversation between the malware and its server, but also makes sure the malware is talking to the attacker’s server and not a blackhole controlled by malware researchers,” Emsisoft experts noted in a blog post.
Finally, CryptoLocker looks for the aforementioned files and encrypts them using AES. Unfortunately, it’s impossible to decrypt the files without the AES key, which is stored on the C&C server and accessible only to the attacker.
However, users are advised not to pay up. Remove the infection with an antivirus program and restore the encrypted files from a backup, assuming you have one.
 14 DAY TRIAL //
14 DAY TRIAL //