Cybercriminals have started a new trend for conducting distributed denial-of-service (DDoS) attacks and rely on a type of DNS (Domain Name System) amplification that leverages text records for making the operation more effective; in some campaigns, parts of a press release from the White House have been observed by researchers.
The tactic is not new, but more and more incidents of this sort have been recorded by the PLXsert (Prolexic Security Engineering and Research Team) of Akamai, which observed it in an October 4 incident.
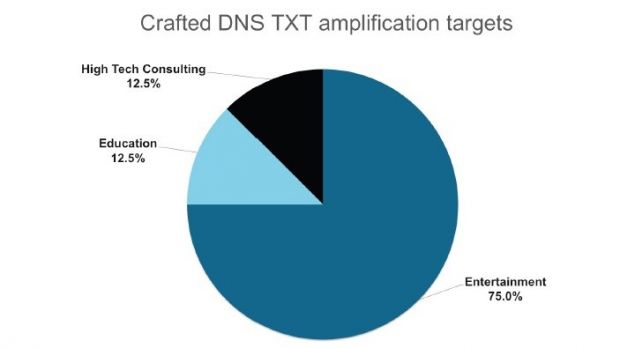
The entertainment sector is the most targeted
“Attackers have used large TXT records in reflection attacks in the past. Previous victims of DNS amplification attacks using TXT records include sites such as isc.org and many .gov sites. With this new threat, malicious actors are now crafting the TXT records to provide the largest response size possible, thereby having as much impact as possible,” a report from the researchers informs.
A DDoS attack is designed to bring a service down by delivering a large amount of requests to its server. When the information can no longer be processed, the machine can no longer do its job
According to PLXsert, the most targeted entities are from the entertainment (75%), education (12.5%), and high tech consulting (12.5%) sectors.
The snippets of the official text originate from the guessinfosys.com domain, and are used in what is called a DDoS reflected attack. Cybercriminals often use intermediate victims to reflect the bad traffic to their target.
Largest incident lasted for more than 15 hours
In the observed incidents, the systems from PLXsert revealed that DDoS attacks leveraging the DNS TXT amplification technique was involved in longer-lasting events (more than five hours), with the most serious such event peaking at over 15 hours.
The statistics gathered from the incidents show that the source port used for the attacks is 53, while the targeted one is 80, but it can also be a random one.
A DNS amplified DDoS incident relies on sending a request to a server from the spoofed IP address of the victim. Thus, when the server returns the response, which is larger than the initial request, the packets are sent to the victim, causing a denial-of-service condition. It appears that the peak bandwidth was recorded by PLXsert at 4.3 Gbps.
Researchers say that using an access control list (ACL) should be a good form of defense, but only if there is more bandwidth than the attack can generate.
 14 DAY TRIAL //
14 DAY TRIAL //