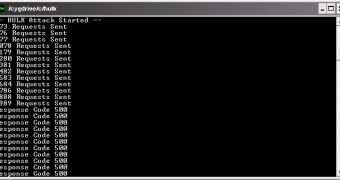
Barry Shteiman, a principal security engineer at Imperva, the owner of the Sectorix blog, and a self-proclaimed “nerd” has released a Python-based web server denial-of-service (DOS) tool called HULK (Http Unbearable Load King).
“For a while now, I have been playing with some of the more exotic tools, finding that their main problem is always the same… they create repeatable patterns. too easy to predict the next request that is coming, and therefor mitigate. Some, although elegant, lack the horsepower to really put a system on its knees,” Shteiman wrote.
As a result, he decided to put his knowledge to good use and create a DOS tool. Of course, the HULK has been developed for educational and research purposes only.
So how does it work?
Basically, the HULK generates unique HTTP requests that cause a large load on the server, making it run out of resources. By generating unique requests, the caching engines are bypassed and the task is put on the server’s shoulders.
Among the techniques the expert utilized we find reference forgery, unique transformation of URLs, the obfuscation of the source client, and the use of the no-cache parameter.
The tests have shown that a web server running Microsoft IIS7 with 4 gigabytes or RAM goes down in less than one minute, the requests being sent from a single client.
Shortly after the HULK was released, security researchers from Trustwave’s Spider Labs have created their own Marvel super hero, THOR, to show how the cleverly crafter requests made by the DOS tool could be counterattacked.
THOR (Thumping Http Obvious Requests) is actually represented by SpiderLabs’ ModSecurity defense rules.
“While the HULK tool does achieve its goal of randomizing the payloads of various headers, it is still quite easily identifiable due to the request header ordering of the requests,” the experts wrote.
They demonstrated that the unique fingerprint created by HULK can be added to a ruleset that can trigger the termination of the connection, and the termination of the DOS tool.
 14 DAY TRIAL //
14 DAY TRIAL //