Independent security researcher Shadab Siddiqui provided us with information regarding a couple of important websites that contain cross-site scripting (XSS) vulnerabilities. More specifically, he found this type of flaws in the official sites of NEC (nec.com) and Udemy (udemy.com).
The site owned by NEC, the company supplying government agencies and private sector companies with IT services, equipment and products for platforms and carrier networks, turns out to be highly vulnerable.
The expert identified XSS vulnerabilities on at least two of their webpages and provided us with screenshots to prove his finds.
Udemy, an online knowledge sharing site, was also discovered to contain XSS and other types of flaws, but fortunately for their customers, they rushed to patch up the security holes.
“It’s quite vulnerable. It had many other vulnerabilities like directory listing, file upload vulnerability etc, but after I informed them about the vulnerability they patched it, but didn’t even had the courtesy to reply me with a thanks,” Siddiqui told us.
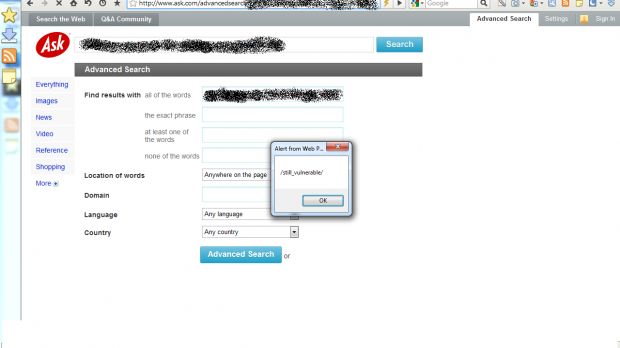
It turns out that after hackers disclosed a large number of weaknesses that were present in their site, Ask patched up some of them, but a lot of them still exist.
“ASk.com has patched few of the XSS bugs but there are still lots of them left out there in spite it has 4-5 million hits per month. And being a big company they have such a low security level that even after being informed by TeamHav0k they haven't fully patched their website.”
Since XSS vulnerabilities in sites are highly common, but also highly dangerous, we’ve asked the expert to explain the risks that hide behind such vulnerabilities.
“XSS vulnerabilities are both unsurprisingly common and usually quite easy to spot(in most cases). Despite the situation, XSS isn’t often concerned as a dangerous security risk. There are different types of XSS like non-persistent, persistent, DOM based,” he explained.
He also highlighted the fact that these vulnerabilities can be used for operations such as stealing sessions, manipulating files on the victim’s computer, recording keystrokes and sending them back to the attacker, stealing files, probing company Intranets, and performing brute force password cracking through the victim’s compromised browser.
“The dangerous thing about XSS is its completely platform independent. Whereas other attacks require a specific operating system or database version to work, JavaScript code runs in virtually every browser on every system.
“And the best part is that XSS open doors to many other vulnerability like CSRF etc. which in turn is a deadly weapon if used by right minds,” Siddiqui concluded.

 14 DAY TRIAL //
14 DAY TRIAL //