On February 13, FireEye reported that cybercriminals were actively exploiting an Adobe Reader zero-day in an effort to spread malware. Experts from Kaspersky and Hungarian security firm CrySyS Lab have found that the same zero-day is being actively used to target high-profile organizations.
Researchers have discovered that the threat, dubbed MiniDuke because of its similarities with Duqu, has been used by cybercriminals to target 59 unique victims located in 23 countries, including Brazil, Bulgaria, Georgia, Germany, Israel, Japan, Latvia, Lebanon, Lithuania, Montenegro, Russia and the UK.
In Ukraine, Belgium, Portugal, Romania, the Czech Republic and Ireland, the malware has been spotted on the systems of government organizations. In Hungary, it has been identified on the networks of a social foundation and in the United States, on the computers of think tanks, a research institute and a healthcare provider.
Kaspersky experts say that the large number of high-profile victims makes the campaign as notable as the now-infamous Red October operation.
The malware is spread via cleverly crafter PDF documents that cover topics related to NATO, Ukraine’s foreign policy, or a human rights seminar.
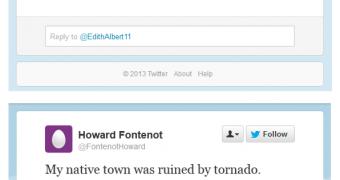
Once it’s activated, the malware uses an interesting technique to communicate. It contacts certain Twitter accounts which have posted encrypted strings that contain an “uri!” identifier (see screenshot).
This encrypted identifier contains the details of a command and control (C&C) server.
“Based on our experience, this is a unique and very strange attack. The many different targets hit in separate countries, together with the high profile appearance of the decoy documents and the weird backdoor functionality indicate an unusual threat actor,” Kaspersky explains in a detailed report.
“Some of the elements remind us of both Duqu and Red October, such as the minimalistic approach, hacked servers, encrypted channels but also the typology of the victims.”
 14 DAY TRIAL //
14 DAY TRIAL //