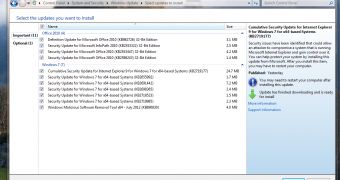
On July 10th, Microsoft announced the release of a new batch of security updates for some of its products, in an attempt to fix a series of issues that these were affected by.
Nine security bulletins were included in the new update – three of which were rated Critical, while six Important – patching a total of 16 vulnerabilities.
Microsoft Windows, Internet Explorer, Visual Basic for Applications, and Microsoft Office were the affected Microsoft products, the company explains.
The most important of the Critical bulletins was MS12-043, destined to resolve a security issue in Microsoft XML Core Services, which could have allowed for Remote Code Execution on a target machine.
The breach was found to affect Microsoft Windows, Microsoft Office, Microsoft Developer Tools, and Microsoft Server Software.
There was also a Cumulative Security Update for Internet Explorer (bulletin MS12-044), which was meant to resolve two vulnerabilities in the browser, both of which could have led to Remote Code Execution.
The third Critical bulletin (MS12-045) fixes a security hole in Microsoft Data Access Components, also resulting in Remote Code Execution, provided that a user visited a specifically crafted webpage.
The first of the Important bulletins in the new security update, MS12-046, fixes an issue in Visual Basic for Applications that could allow for Remote Code Execution and which affected Microsoft Office, Microsoft Developer Tools.
For an attack to be successful, a user has to open “a legitimate Microsoft Office file (such as a .docx file) that is located in the same directory as a specially crafted dynamic link library (DLL) file,” Microsoft explains.
“An attacker could then install programs; view, change, or delete data; or create new accounts that have full user rights. If a user is logged on with administrative user rights, an attacker could take complete control of the affected system.”
MS12-047, the second Important bulletin, resolves an issue in Windows Kernel-Mode Drivers that could have resulted in elevation of privilege.
A vulnerability that affects Windows Shell was also patched in this update. It could allow “remote code execution if a user opens a file or directory with a specially crafted name.”
Additionally, the July 2012 security update fixes an issue in TLS that could allow for information disclosure, as well as six vulnerabilities in SharePoint, which could allow for elevation of privilege.
The last bulletin in the new update suite is destined to patch a hole in Microsoft Office for Mac that could allow for elevation of privilege. It requires for the attacker to place a malicious executable on the affected system, and for a user to run the executable.
These updates will arrive on all systems that have the Automatic Updates feature turned on. Users who don’t have the option enabled are advised to update their systems manually as soon as possible.
 14 DAY TRIAL //
14 DAY TRIAL //