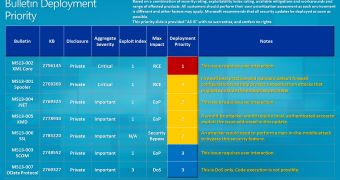
Microsoft has recently rolled out the first Patch Tuesday updates of 2013, trying to patch two critical vulnerabilities and five important flaws found in its software.
The first critical vulnerability, labeled by Microsoft as MS13-001, is actually a security flaw in the Windows 7 and Windows Server 2008 R2 print spooler service that would allow an attacker to get control of an affected operating system.
“The vulnerability could allow remote code execution if a print server received a specially crafted print job,” the company explained in its security bulletin summary for January 2013.
The second critical glitch concerns the Microsoft XML Core Services and is supposed to patch a flaw that would allow a hacker to run malicious code on a vulnerable system when the user loads a compromised website in Internet Explorer on any Windows version.
“An attacker would have no way to force users to visit such a website. Instead, an attacker would have to convince users to visit the website, typically by getting them to click a link in an email message or Instant Messenger message that takes the user to the attacker's website,” Microsoft said in the post.
The five important patches fix flaws in Microsoft System Center Operations Manager 2007/R2, .Net Framework, Windows Vista, Server 2008 R2, Server 2012, Windows RT and Windows XP.
“We encourage customers to start 2013 on a secure foot by applying these security updates to help ensure protection in the New Year. Customers who have Automatic Updates enabled will receive these protections automatically and do not need to take action,” Dustin Childs, group manager, Microsoft Trustworthy Computing, told us in a statement.
As always, all patches will be delivered via the Windows Update built-in feature, but those who wish to download and deploy them manually can find all of them on Microsoft’s download center.
 14 DAY TRIAL //
14 DAY TRIAL //