Security specialists have recently discovered a virus that makes its way into the BIOS, making it very hard to get rid of using current commercial anti-virus solutions.
The virus called Mebromi seems to be focused towards Chinese users, especially Award BIOS owners, but this doesn't mean that the rest of the world is safe, as this could represent a gate opener for hackers who want to make sure our computers remain under their control.
A full description of the way Mebromi functions was posted on the Webroot Threat Blog, giving us an insight on how this malicious element makes its way to the very core of a computer.
The BIOS rootkit, an MBR rootkit, a kernel mode rootkit, a PE file injector and a Trojan downloader are the elements encapsulated in this potentially destructive malware, which at the moment is unable to cause any damage to machines running 64-bit operating systems if the user privileges are limited.
The whole thing starts with a few files that try to access the kernel to load the virus's own kernel driver that will later generate the serious part of the infection.
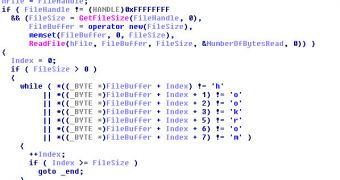
After it successfully infects the BIOS using a file called Cbrom.exe, which is a legitimate tool developed by Phoenix Technologies designed to modify the Award/Phoenix system's ROM binaries, it moves to infecting the master boot record of the device.
The winlogon.exe or wininit.exe files are also corrupted and injected with codes that will generate the download of additional infections.
“Storing the malicious code inside the BIOS ROM could actually become more than just a problem for security software, given the fact that even if an antivirus detects and cleans the MBR infection, it will be restored at the next system startup when the malicious BIOS payload would overwrite the MBR code again,” stated a researcher from Webroot.
“Developing an antivirus utility able to clean the BIOS code is a challenge, because it needs to be totally error-proof, to avoid rendering the system unbootable at all. The job of handling such specific system codes should be left to the developers of the specific motherboard model, who release BIOS updates along with specific tool to update the BIOS code,” he further revealed.
It seems as these types of threats should present somewhat of a concern, but the fact of the matter is that it's a difficult task for a hacker to develop a malicious program that could affect all types of computers. So for now, we should much rather fear the present dangers that lurk behind our every click, in an attempt to take over our computers.
 14 DAY TRIAL //
14 DAY TRIAL //