Man-in-the mobile (MITMO) attacks powered by pieces of malware such as Tatanga and SpyEye (SPITMO) have been spotted targeting users from Portugal, Spain, the Netherlands and Germany.
It all starts with web injections in the browsers of Windows users. The injections are utilized to convince the potential victims to install a shady bank security application onto their mobile phones.
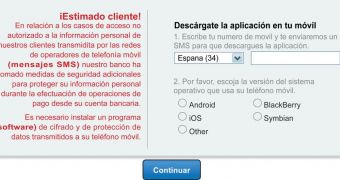
For the user, it looks like the financial institution is requesting the installation of the app.
First, the victim is asked to choose the name of the operating system running on his/her mobile device. The list includes iOS, BlackBerry, Android and Symbian, but for the time being, only those who use Google’s operating system are affected.
In case the victim chooses iOS, BlackBerry or Symbian, nothing dangerous happens. A message appears, telling the user that his/her device doesn’t require any additional protection.
On the other hand, it’s a whole different story with Android.
Android customers are requested to provide their phone numbers. Once they comply, they receive an SMS that contains a link to the alleged security app. The same text message also contains a code that’s presumably needed to activate the product.
After the shady software is installed onto a device, the attackers gain access to all SMS traffic. This means that they can obtain transaction authorization codes sent by the bank to the customer, allowing them to make fraudulent transfers.
“This discovery confirms that Man-in-the-Mobile attacks are focusing primarily on Android devices. Multiple studies show that Android devices account for more than 60% of smartphone market in the targeted countries,” Amit Klein, CTO of Trusteer explained.
“Android popularity and the relative ease of developing and distributing Android applications are probably the reasons why Cybercriminals have singled out this particular platform for mobile malware attacks.”
 14 DAY TRIAL //
14 DAY TRIAL //