ESET researchers have come across an Apache module that's being used to inject malicious content into the webpages served by compromised Linux servers. The module’s main goal is to spread the bank account-stealing malware known as Zbot, or ZeuS.
According to experts, the module, identified as Linux/Chapro.A, is capable of serving any type of content. However, it appears to be serving the Win32/Zbot Trojan, which mainly targets the customers of European and Russian financial institutions.
Linux/Chapro.A has some clever mechanisms that allow it to remain undetected by system administrators. For instance, it avoids web browsers that are known to be less vulnerable and it avoids serving the malicious content multiple times.
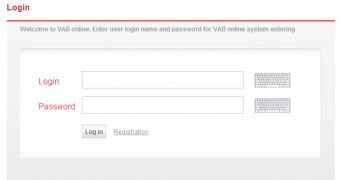
The ZeuS variant that’s being served by the module ensures that whenever the victims access a banking website, a replica of the legitimate page (minus all the warning messages) is presented.
After users log in, the malware injects a pop-up screen which asks users for their card numbers, CVV codes and other sensitive details, and sends them all back to the botnet operator.
Interestingly, the iframe injected by Linux/Chapro.A points to a Sweet Orange exploit kit landing page, the one that is advertised as being capable of infecting 10,000 new computers daily.
Experts say that there appear to be no links between Chapro and the Linux rootkit analyzed back in November by Kaspersky and Crowdstrike, despite the fact that they have the same goals. On the other hand, it’s very similar to the malicious element identified on underground forums by Dancho Danchev around three weeks ago.
ESET hasn’t identified any other installations of this Apache module in the wild, but experts have found that thousands of users have accessed the Sweet Orange exploit kit before the company could block access to the server.
 14 DAY TRIAL //
14 DAY TRIAL //