Security solutions provider McAfee has released its Threats Report for the fourth quarter of 2012.
The study shows that a larger number of industries are targeted by cyberthreats. The number of password-stealing Trojans increased by 74% in the last quarter of 2012 and pieces of malware such as Citadel are now being utilized to target other sectors, not just the financial services one.
It turns out that the efforts of law enforcement have paid off. The company has identified a decline in the number of infected systems controlled by botnet operators.
On the other hand, cybercriminals have started replacing botnets with suspicious URLs. McAfee discovered 4.6 million new suspect URLs per month, 95% of which were found to be hosting exploits and malware.
Interestingly, McAfee believes that Master Boot Record (MBR) attacks a will become a primary vector for cybercriminal operations in 2013. However, so far, the number of pieces of malware that attempt to hide their presence by infecting the MBR is fairly low.
In Q4 of 2012, the number of malware samples signed with digital certificates has doubled, which shows that criminals see this as a highly efficient method to bypass standard security measures.
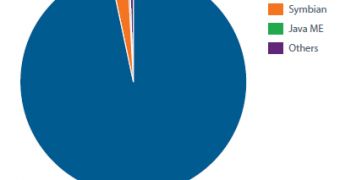
As far as mobile malware is concerned, in 2012, the number of such threats multiplied 44 times compared to the previous year. As expected, the Android platform continues to be targeted, an 85% increase being recorded in the fourth quarter alone.
“We are seeing attacks shifting into a variety of new areas, from factories, to corporations, to government agencies, to the infrastructure that connects them together,” said Vincent Weafer, senior vice president of McAfee Labs.
“This represents a new chapter in cybersecurity in that threat-development, driven by the lure of financial industry profits, has created a growing underground market for these cybercrime weapons, as well as creative new approaches to thwarting security measures common across industries.”
The complete McAfee Threats Report: Fourth Quarter 2012, is available here.
 14 DAY TRIAL //
14 DAY TRIAL //