Last week, Trend Micro researchers came across a piece of malware designed to steal image files from the infected computers and send them back to its master. In the meantime, other security firms have also analyzed the threat and they say it might return later as part of a sophisticated attack.
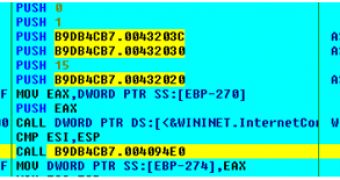
The Trojan is specialized in stealing .jpg, .jpeg and .dmp (Windows memory dump) files and uploads them to an FTP server whose address is hardcoded into the malware.
McAfee’s Research Scientist Niranjan Jayanand reveals that there could be two reasons for which the malicious element steals .dmp files.
One of them could be the fact that the malware’s developers have made a mistake when writing the code. They might have actually wanted to collect .bmp image files, but because of the typo the Trojan is collecting .dmp files.
The second variant is that this is only the first stage of a soon-to-be sophisticated threat and the information from the .dmp files is utilized to collect information about the vulnerabilities that plague the targeted machines.
On the other hand, Sophos experts have also examined the threat that they call Troj/PixSteal-A. They reveal that the crooks might be hoping to obtain scanned copies of sensitive documents such as passports, or company papers.
One of the files they found on the FTP server in question was called “Google_Talk_1.0.0.104_121002-170904.dmp.” Sophos Labs researchers believe that such files might be targeted because they can contain instant messaging conversations.
In this case, experts provide some interesting advice. They emphasize the fact that FTP access should be blocked from the firewall.
“FTP should have died a long time ago and you can help. Just refuse to use it. Web host require FTP for your website? FIND A NEW HOST. Your password should never be transmitted in plain text, therefore you should never use FTP,” Sophos’ Chester Wisniewski explained.
As of November 5, the FTP server utilized by the malware is dead.
 14 DAY TRIAL //
14 DAY TRIAL //