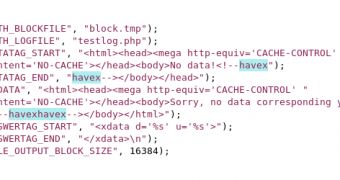
Security researchers found that cybercriminals adopted new methods for distributing Havex, a remote access Trojan (RAT), and that their attention shifted towards industrial control systems (ICS).
Havex has been previously used to compromise systems in the energetic sector, but this spring, it was observed that bad actors managed to implant trojanized versions of the software on ICS/SCADA manufacturer websites in order to infect the computers it was installed on.
In monitoring the activity of the Havex malware family, F-Secure collected a total of 88 variants of the RAT, all having the capability to gain access to the targeted machines or networks, as well as to retrieve information from them.
Cybercriminals used compromised websites and blogs as command and control (C&C) servers, which limited their traceability. The researchers investigated 146 servers that were contacted by the malware and the result was the discovery of about 1500 IP addresses for infected machines.
Provided that the criminals deliver the RAT in software for ICS/SCADA systems, it is possible that they are now seeking control of the systems.
There are multiple types of ICS, among them being supervisory control and data acquisition (SCADA) systems, distributed control systems (DCS) and programmable logic controllers (PLC), all used in industrial sectors like electrical, water, gas, oil and data.
“This indicates that the attackers are not just interested in compromising the networks of companies they are interested in, but are also motivated in having control of the ICS/SCADA systems in those organizations,” writes Daavid Hentunen, senior researcher at F-Secure.
Apart from compromising the ICS vendor to reach the victim, the payload is delivered through spam and various exploit kits.
The attackers seek vulnerabilities in the software run on the website in order to replace the legitimate installation file of the ICS application. Customers download it from a trusted source and become victims as soon as it is installed.
“Our research uncovered three software vendor sites that were compromised in this manner. The software installers available on the sites were trojanized to include the Havex RAT. We suspect more similar cases exist but have not been identified yet,” says Hentunen.
The investigation revealed that the vendors are from Germany, Switzerland and Belgium and are involved in developing programs and appliances for different industrial usages.
By running a trace of the IP addresses that contacted the command and control servers, the security firm detected some of the victims, the activity of all of them being related to the development or use of industrial applications or machines.
Most of the organizations affected are based in Europe (Germany, France and Russia) and carry out technology research activities, manufacture industrial machines and applications, or specialize in structural engineering.
F-Secure says that they also noticed a California-based company contacting the server and sending data.
Provided all this, the evidence of cyber-espionage activity is clear. The group behind these attacks collects information about the ICS hardware connected to the compromised computer, which is a sign that they “ have direct interest in controlling such environments.”
 14 DAY TRIAL //
14 DAY TRIAL //