Twitter, like most other big web companies, has been the target of many, sometimes successful attacks. The biggest and most recent is an attack that managed to infiltrate Twitter's inner network and snatch records on some 250,000 users.
No crucial data is believed to have been smuggled out, but the attack was a wake-up call for Twitter, if it ever needed one.
Twitter's head of security, Bob Lord gave a presentation at Hack in the Box 2013, currently underway in Amsterdam. Our very own Eduard Kovacs is on the show floor and attending the presentations, so expect more from him and Hack in the Box to follow.
During his presentation, Lord talked about how he and Twitter are tackling the issue of internal security, especially in the light of the recent attack.
His approach is to create a security culture inside the company rather than just give employees security training, though training is a big part of that of course.
Lord focuses on new employees since they're the most impressionable, in a good way. There's a greater chance that what they learn on the first day will stick with them, so he goes through the security training as soon as possible, in person when possible.
One way Lord has tried to improve the security habits of employees is via password managers. There's a large trend against using passwords as security measures, but it's going to be a long while before they're phased out.
Until then, a password manager can help users keep and create strong passwords for all the accounts they use without actually having to remember them all or worse, keeping them written down somewhere.
Another thing Lord focuses on in order to secure Twitter from the inside out, is followup. He stresses the importance of data, of actually taking the time to learn how employees, or users for that matter, use the security tools at their disposal.
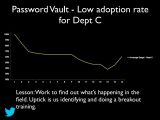
Twitter, for example, studied how often employees used password managers to store passwords after their initial instructions. What it found was that, initially, as the weeks went by some employees from every department would stop using the tool.
So Twitter looked at the problem, did some more training where it was needed, and then saw a significant uptake in the number of people using the "password vault," whereas the numbers had been dropping consistently before that.
Twitter also found that the people who stuck with the password managers for the first few weeks would get used to them and become long time users.
Another way to test whether employees really are staying safe is via phishing campaigns. Twitter would send out fake phishing emails to employees to see if they took the bait.
A number of people from each department, more from some departments, fewer from others, would click on the link which would have been infected if it had been a real phishing email.
For Twitter, Bob Lord revealed, this has been a learning experience, they are learning how to teach employees to stay safe just as the employees themselves are learning to stay safe.
As with anything else, key to this has been studying how effective the training had been and how to improve the problem areas.

 14 DAY TRIAL //
14 DAY TRIAL //