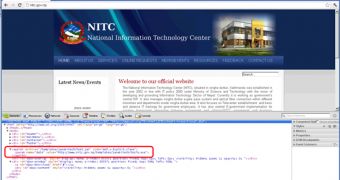
The site of the National Information Technology Center (nitc.gov.np), and the one of the Office of the Prime Minister and Council Minister (opmcm.gov.np) – both owned by the government of Nepal – have been found to serve visitors a backdoor known as Zegost (Gh0st).
The campaign relies on exploiting the same Java vulnerability that had been leveraged a few months ago in the attack on the site of Amnesty International UK, Websense experts report.
There are several clues which indicate that these attacks may be linked to other cybercriminal operations, such as the ones that targeted Tibetans and Uyghurs.
Primarily, all the compromises used pieces of code that hadn’t been obfuscated, taken from the Metasploit framework. The rest of the hints that linked the attacks were provided by the remote administration software and the command and control servers it was connecting to.
The technical analysis performed by the experts began with determining that the file dropped on the site of NITC – tools.exe – was similar to the one dropped on the OPMCM site. The executable was served after the exploit code in the malicious Java JAR file, injected into the hijacked webpage, had been successfully run.
Tools.exe has been identified as being a variant of the Zegost backdoor toolkit, which, according to AlienVault, has been utilized on numerous occasions in targeted attacks in Asia.
By running the malicious element in a sandbox environment, the researchers have been able to determine that its command and control (C&C) server is located at the “who.xhhow4.com” domain. “Hhow4.com” is the domain that has been used by the C&C in the Amnesty International UK incident.
A noteworthy aspect is that the backdoor is signed with a valid certificate issued to 360.cn by VeriSign. It’s uncertain how the digital certificate of a Chinese ISP has ended up being used to sign malware, but it’s a clear indication that the method has become a popular way to evade antivirus detection.
 14 DAY TRIAL //
14 DAY TRIAL //