The fight against spammers and scammers is never over. As Gmail spam filters got better, attackers looked at other ways of getting through. A very popular method for bypassing the spam filters is to break into legitimate Gmail accounts and then use them to spam their contacts.
This method started becoming increasingly popular since 2010, but Google has countered with new ways of protecting user accounts.
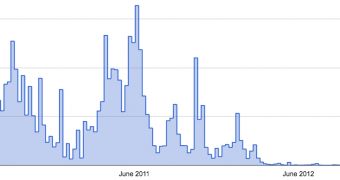
In fact, Google has been effective at it that it's reduced the number of compromised accounts by 99.7 percent since 2011, at the peak of these attacks, the company revealed in a rather self-congratulatory blog post, a warranted one perhaps.
A common way of trying to break into an account is getting ahold of email and password combinations from compromised sites. Because many people reuse their passwords, the data could be used to log into the Google accounts.
"With stolen passwords in hand, attackers attempt to break into accounts across the web and across many different services. We’ve seen a single attacker using stolen passwords to attempt to break into a million different Google accounts every single day, for weeks at a time. A different gang attempted sign-ins at a rate of more than 100 accounts per second," Google explained.
When users attempt to log into their accounts, either from their computers, or automatically via a mobile app and so on, Google doesn't just check to see if the password is accurate, it also looks at some 120 factors to try to determine whether the login attempt is a legitimate one or a fraudulent one.
If its algorithms have reasons to suspect foul play, users may be asked their security question or for some additional data, like the phone number associated with the account.
This mostly stops account hijackers in their place, since they don't have that information and even if they could obtain it, for many it's a matter of scale, it doesn't pay off to do all the extra work to gain all the extra data.
 14 DAY TRIAL //
14 DAY TRIAL //