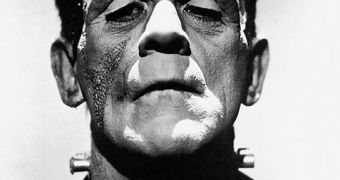
Vishwath Mohan and Kevin Hamlen of the University of Texas have created Frankenstein – a software that is able to develop malware by combining various pieces of code taken from common applications.
Once Frankenstein finds itself on a computer, it starts looking for specific pieces of code from programs such as popular web browsers and even Notepad. These elements, called gadgets, ultimately create malware that’s capable of performing certain tasks.
For now, the researchers have created two simple algorithms and, although they couldn’t develop a “full malware,” they were able to demonstrate that the technique could be utilized to develop something truly malicious, New Scientists reports.
So how does it work? For instance, if the newly created malware must steal data, Frankenstein looks for pieces of code that are able to perform the task. To ensure that antivirus programs see it as something different on each computer it infects, the gadgets are not always taken from the same programs.
If you’re wondering how many gadgets the monster can obtain from regular software, the answer is 100,000 from just three applications. This means that the combinations could be infinite, given the fact that the blueprints which tell it how to piece everything together are provided.
The researchers say that such a virus could be efficiently utilized to penetrate the networks of an organization which uses unknown antivirus solutions (you’re probably thinking Iran).
On the other hand, while this type of malware could be virtually impossible to detect by signature-based antivirus, it’s well known that modern day solutions don’t rely only on the classic signatures.
They also secure computers by analyzing the behavior of files, data transfers, communications and anything else that could help in identifying the malicious nature of a piece of software.
 14 DAY TRIAL //
14 DAY TRIAL //