Researchers who have analyzed SSL certificates and the way they’re validated claim that vulnerabilities caused by poor SSL implementation allow cybercriminals to launch man-in-the-middle (MitM) attacks against non-browser software.
A few weeks ago, experts from German universities uncovered that MitM attacks could be launched against a considerable percentage of Android apps because they utilized SSL/TLS in an inadequate or incorrect manner.
Now, researchers from the University of Austin, Texas, and Stanford University have released a study to demonstrate that SSL certificate validation is “completely broken” in a number of security-critical applications and libraries.
The paper, called “The Most Dangerous Code in the World: Validating SSL Certificates in Non-Browser Software,” reveals that in many cases these vulnerabilities are caused by poorly designed APIs.
The vulnerable software includes Amazon’s EC2 Java library, PayPal’s and Amazon’s merchant SDKs – the ones responsible for transmitting payment details from websites to payment gateways –, and numerous integrated shopping carts, including osCommerce and ZenCart.
Java Web-services middleware, Chase mobile banking and several Android libraries and apps have also been found to contain this security hole.
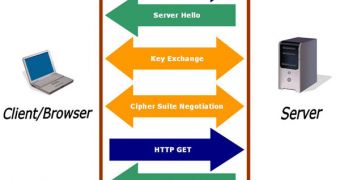
SSL connections are normally designed to prevent cybercriminals from intercepting sensitive data. However, according to experts, because certificate validation is broken, attackers can launch MitM attacks and retrieve the valuable information.
In order to address these issues, the researchers recommend the development of “better black-box testing and code analysis tools for discovering errors in SSL connection establishment logic.”
They also recommend the use of “formal verification techniques and programming language support for automatically checking whether applications use SSL libraries correctly and not misinterpret the meaning of critical options and parameters, and design of better APIs for SSL and other secure networking protocols.”
Experts agree. GlobalSign’s CTO Ryan Hurst has told Softpedia that companies need to invest in best practices in order to address these issues.
“Today’s security and protocol APIs were designed for specialists that understood the feature-rich, yet confusing design options that the associated technologies allow,” Hurst said.
“However, application developers do not have time to become experts in these foundational technologies nor should they be required to. API’s must evolve to meet the demands of today’s developers, allowing for easy design with minimal investment.”
The CTO points out that recent security incidents – such as the ones that affected eHarmony and LinkedIn – highlight the fact that many large organizations are still utilizing weak cryptographic algorithms to secure passwords.
“It is also worth noting that many browsers have their own issues in their use of certificates and SSL as they have reallocated those resources to feature development rather than security,” he added.
Many of these problems can be addressed if security is incorporated not just in the testing phase, but also in planning and development. Also, security assumptions must be continually reevaluated.
Finally, as the researchers have highlighted, API developers must also take security into consideration before creating their products.
GlobalSign is planning to release a free service that will allow organizations to assess the strength of their SSL. The service will also offer guidance on how effectiveness can be increased.
 14 DAY TRIAL //
14 DAY TRIAL //