Vulnerability Lab researchers have provided Softpedia with the details of an iOS 6.1 vulnerability that could be exploited to bypass the password lock (code lock) on iPhones and iPads, allowing an attacker to gain access to everything that’s stored on the device.
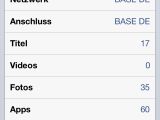
“The vulnerability is located in the main login module of the mobile iOS device (iPhone or iPad) when processing to use the screenshot function in combination with the emergency call and power (standby) button,” Vulnerability Lab explained.
“The vulnerability allows the local attacker to bypass the code lock to access the iTunes or connect via USB when a black screen bug occurs.”
According to Vulnerability Lab, the security hole they discovered was reported to Apple around 4 months ago.
Benjamin Kunz Mejri, the founder and CEO of Vulnerability Lab, has told Softpedia that Apple hasn’t responded to their reports and that the company didn’t take any steps during these four months to address the flaw.
This is why they’ve published a proof-of-concept video which shows how the flaw can be exploited. The experts say iOS users should test the login and emergency function again after the next Apple iOS kernel update.
The details of the vulnerability and the steps to reproduce it can be found here.
The details of a similar vulnerability were made public at the end of January by other researchers.
These aren't the first issues of this kind. Such a flaw affected iOS 4, but now the bug appears to have resurfaced. Apple representatives have told All Things D that they’re currently working on a fix for the first bug.
Here is the video in which Vulnerability Lab researchers demonstrate both vulnerabilities:
Updated to clarify that Vulnerability Lab has discovered only one of the vulnerabilities.

 14 DAY TRIAL //
14 DAY TRIAL //