In October 2013, some experts announced their intention to audit TrueCrypt, the open source file and disk encryption software, to see if it was really secure. The first phase of the audit has been completed and the results are in.
According to the report from iSEC Partners, the company in charge of reviewing the software, a total of 11 issues have been discovered. Four of them are medium-severity, another four are low-severity and the rest are “informational” issues.
iSEC says the source code for the bootloader and the Windows kernel driver does “not meet expected standards for source code.” The issues include the use of insecure or deprecated functions, lack of comments, and inconsistent variable types.
On the other hand, the online documentation does contain good recommendations on how to use TrueCrypt and a detailed description of the application’s functionality.
On the bright side, the auditors say they haven’t found any evidence of “backdoors or otherwise intentionally malicious code in the assessed areas.”
The vulnerabilities they have identified appear to be a result of bugs that have been introduced unintentionally.
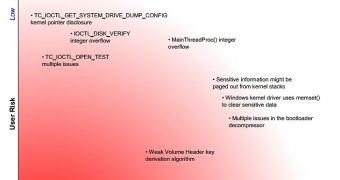
The list of vulnerabilities includes a weak Volume Header derivation algorithm, multiple issues in the bootloader decompressor, sensitive information paged out from kernel stacks, and the fact that the memset() function is used by the Windows kernel driver to clear sensitive data.
These are the medium-severity flaws that put user information at risk. Successful exploitation could lead to legal implications, a negative impact on the client’s reputation and moderate financial impact.
The list of low-severity bugs includes integer overflows in IOCTL_DISK_VERIFY and MainThreadProc(), kernel pointed disclosure in TC_IOCTL_GET_SYSTEM_DRIVE_DUMP_CONFIG, and multiple issues in TC_IOCTL_OPEN_TEST. In the case of these vulnerabilities, the risk is relatively small or considered not important.
iSEC recommends that the Windows build environment is updated because it depends a great deal on tools and software packages that are difficult to obtain from trustworthy sources. Once this is done, all binaries, with all security features enabled, should be rebuilt.
In addition to updating the build environment, experts also recommend that the quality of the code should be improved because the way it is now makes it difficult to review and maintain TrueCrypt.
Phase two of the audit focuses on cryptanalysis. This second phase will also probably take several months to complete.
A full report on phase one of the TrueCrypt audit can be found on the opencryptoaudit.org website.
 14 DAY TRIAL //
14 DAY TRIAL //