Have you ever dreamed of having the ultimate protection for your computer? Of course you did, especially if you have sensitive files that you don't want anybody to see. Well, your dream can come true with the help of an encrypted filesystem. The encrypted filesystem is one that resides on an encrypted disk or partition. There are many methods to create such an encrypted filesystem, but today I am going to teach you an easy method to use an encrypted filesystem to protect your data.
There are also a lot of tools to encrypt your filesystem, all free, but some of them have weaknesses. So, I've chosen the dm-crypt (device-mapper crypto target) which provides transparent encryption of block devices with the help of cryptoapi, that can be found in the new Linux 2.6 kernel.
We will use a 256-bit AES (Advanced Encryption Standard) encryption, so make sure that your kernel has AES support loaded. Open a console and type:
~$ cat /proc/crypto name : md5 driver : md5-generic module : kernel priority : 0 refcnt : 1 type : digest blocksize : 64 digestsize : 16
Which is not good! So, if you get the same result, type the following code in order to activate the AES module:
~$ cat /proc/crypto name : aes driver : aes-generic module : aes priority : 100 refcnt : 1 type : cipher blocksize : 16 min keysize : 16 max keysize : 32
name : md5 driver : md5-generic module : kernel priority : 0 refcnt : 1 type : digest blocksize : 64 digestsize : 16
Which shows me that the AES module was successfully loaded. You have to install two more tools, dmsetup and cryptsetup:
~$ sudo dmsetup targets crypt v1.3.0 striped v1.0.2 linear v1.0.2 error v1.0.1
Which shows me that crypt was added to available targets and I can continue with the encryption process.
You need to setup a block device and mount it as an encrypted logical volume. First, let's create a logical volume with cryptsetup and bind the block device to it:
MAKE SURE THE PARTITION IS UNMOUNTED AND EMPTY BEFORE YOU TYPE THE FOLLOWING CODE
You will be asked for a passphrase (twice) so be careful what you type (don't forget it, or you will lose everything on the encrypted partition).
~$ sudo cryptsetup -y create securedata /dev/sdb4 Enter passphrase: Verify passphrase:
Then you should verify if the logical volume was created, so type the following code:
~$ sudo dmsetup ls securedata (254, 0)
Now, if you type:
~$ ls -l /dev/mapper/ total 0 crw-rw---- 1 root root 10, 61 2007-06-12 16:47 control brw-rw---- 1 root disk 254, 0 2007-06-12 17:07 securedata
Create an ext3 filesystem on the virtual block device:
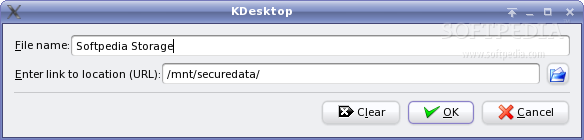
To automatically mount this partition every time you boot-up your PC, add the following link in the /etc/fstab file:
I'll get back soon with another guide on how to have an encrypted Ubuntu operating system. Until then, test this one. Enjoy!

 14 DAY TRIAL //
14 DAY TRIAL //