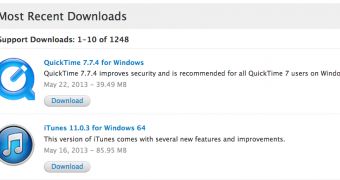
Apple has released QuickTime 7.7.4, a new version of the company’s multimedia framework and media player, for Windows customers. QuickTime 7.7.4 is a security release.
According to the official release notes, the update “improves security and is recommended for all QuickTime 7 users on Windows.”
Apple discloses the full contents of the update in a security advisory on its Support site: “About the security content of QuickTime 7.7.4.”
Here, the Mac maker mentions a dozen vulnerabilities that have been recently discovered in QuickTime for Windows, all of which are addressed in the new version.
All of the bugs affect QuickTime 7.7.3 and older installations of the software on Windows 7, Vista, and XP SP2 or later.
For example, a memory corruption issue lying in the handling of TeXML files could lead to an unexpected application termination or arbitrary code execution by opening a maliciously crafted TeXML file.
Playing a maliciously crafted movie could lead to a similar exploit, because of a buffer overflow in the handling of H.263 encoded movie files.
Such buffer overflows also existed in the handling of “dref” atoms, as well as in the handling of H.264 encoded movie files, MP3 files, Sorenson encoded movie files, JPEG encoded data, QTIF files, “enof” atoms, FPX files, and “mvhd” atoms.
As usual, Apple credits the appropriate parties for discovering and reporting the vulnerabilities. These include Andrea Micalizzi (aka rgod), G. Geshev, Tom Gallagher (Microsoft) & Paul Bates (Microsoft), and Mil3s beep, all working with HP's Zero Day Initiative.
A developer identified as “roob” working with iDefense VCP is also credited for reporting a memory corruption issue in the handling of QTIF files.
System requirements include Windows XP (SP2 or later), Windows Vista, and Windows 7.
The installer supports various languages, including Deutsch, English, Français, Español, Italiano, Nederlands, Dansk, Norsk Bokmål, Polski, Português, Português (Brasil), Pусский, Suomi, Svensk, Chinese, Japanese, and Korean.
 14 DAY TRIAL //
14 DAY TRIAL //