Internauts, especially those who work in a corporate environment, should be on the lookout for an alert that notifies them on a meeting. The simple-looking emails carry a dangerous piece of malware that’s currently detected by only around half of the existent antivirus solutions.
Apparently originating from spoofed LinkedIn or FilesTube addresses such as [email protected] or [email protected], the messages only contain a small piece of text, experts from MX Labs report.
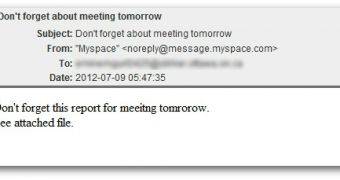
“Don’t forget this report for meeitng tomorrow. See attached file,” it reads.
The “attached file,” called report.zip, contains another element that looks something like Report_Alk_Com-[number].exe.
The executable is a Trojan commonly identified as W32/Trojan3.DUC (Commtouch), Win32:Dropper-gen [Drp] (Avast!), Trojan:W32/Injecter.AO (F-Secure), or HEUR:Trojan.Win32.Generic (Kaspersky).
Experts from Sophos have also analyzed these emails and they highlight the fact that the typos can vary from one version to the other. For instance, in some cases, “meeting” is spelled “meteing” and “tomorrow” is spelled “tomrorow.”
However, the typos may be seen by recipients as a common mistake made by someone who’s in the rush, or who might be writing from a mobile device. In reality, the spelling errors are a way to bypass a company’s email filters which may flag the alerts as being malicious if they’re exactly the same.
Another interesting thing is that Sophos identified the email as coming from [email protected]. This may indicate that the sender’s addresses also vary a lot.
In situations in which a relatively new piece of malware is involved, signature-based antivirus solutions can’t do much to keep you away from trouble. That’s why we recommend that you rely on common sense to avoid falling victim.
The email may look like it’s genuinely coming from a co-worker, but once you see the “report.zip” file or the “report.exe” file, it should be a clear indication that something is fishy.
 14 DAY TRIAL //
14 DAY TRIAL //