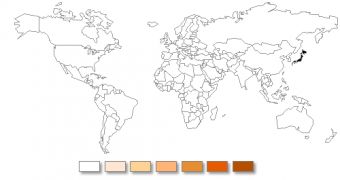
The notorious ZeuS banking Trojan has been around for quite some time now, aiding cybercriminals in stealing the personal and financial details of users whose computers it infects. However, up until recently, the threat hasn’t been used against internauts from Japan.
It’s uncertain why banking Trojans haven’t been used against individuals from Japan, but it could be because of the language barrier.
Over the past months, the National Police Agency of Japan has released numerous alerts to warn bank customers about the threats posed by banking Trojans. Now, Symantec experts have uncovered a variant of ZeuS that’s being utilized to target the customers of five major Japanese banks.
Other than the fact that it’s aimed only at Japanese users, the Trojan’s functionality hasn’t changed.
Once it infects a computer, ZeuS monitors the websites visited by the victim.
When a bank site is accessed, HTML code is injected into the webpage to display the following message (in Japanese): “In order to provide a better service to our customers, we are updating our personal internet banking system. Please re-enter the information that you provided when you first registered.”
The victims are asked to hand over information that can be used by the attacker to access their online banking accounts. The information provided by the user is recorded via ZeuS’s integrated keylogger functionality.
As far as the distribution mechanism is concerned, the cybercriminals use the BlackHole exploit kit to install ZeuS, which is basically the typical way in which the threat is spread.
Symantec’s antivirus solutions and Intrusion Prevention Systems (IPS) are capable of mitigating the threat. Users are advised to always keep their pieces of software updated and try to avoid clicking on shady-looking links or suspicious attachments.
 14 DAY TRIAL //
14 DAY TRIAL //