The easiest way to compromise a large number of websites without putting too much effort into it is by gaining unauthorized access to a hosting server and injecting malicious iframes into the targeted sites’ webpages.
A perfect tool for the job is an Apache 2.x-based module that’s specially designed for the job.
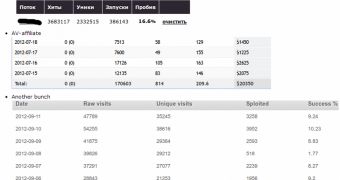
Writing for security firm Webroot, Dancho Danchev explains that one of the tools he has researched can be purchased from the underground market for $1,000 (800 EUR). It’s author advertises it as a highly-efficient tool that’s perfect for spreading scareware.
This particular module deploys some clever techniques in order to ensure that the compromised sites are not easy to identify.
For instance, it hides the iframe URL from search engines, Google Chrome and Linux users.
Another interesting feature allows the module to insert and rotate iframes on all the pages of a particular website.
“The process will only work with a cookie+unique IP in an attempt by the cybercriminal behind the kit to make the process of analyzing the module harder to perform,” Danchev explained.
 14 DAY TRIAL //
14 DAY TRIAL //