Websites running on WordPress that do not have the latest version of the Custom Contact Form component installed are susceptible to remote attacks that can allow downloading and modifying the database.
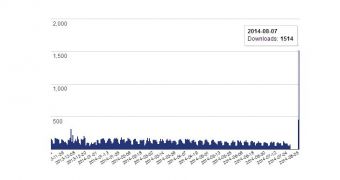
The plugin is designed to permit customization of the contact form without the requirement of any CSS knowledge. Its easy-to-use features make Custom Contact Form a very popular WordPress component, which has gathered more than 620,000 downloads in time; the latest download trend, though lower, still reaches a few hundreds downloads per day.
An attacker could potentially take control of a website “without requiring any sort of privileges/accounts beforehand,” said Marc-Alexandre Montpas from Sucuri. The glitch affects all versions of the plugin except the recently released 5.1.0.4.
It appears that the bug relates to the “adminInit()” function, which could be exploited by cybercriminals in order to create new user accounts with administrator privileges.
The security glitch has been reported to the developer by Sucuri, a company that offers integrity protection solutions for websites. However, no response was returned, and Sucuri turned to the WordPress security team for fixing the flaw.
Custom Contact Form’s development team has announced on the plugin’s website that code contribution from developers is needed urgently, in order to improve the component. Staff shortage may also be the reason behind the lack of response from the team at Sucuri’s bug submission.
This is also why Montpas recommends users to change their option as far as contact form customization is concerned, and opt for solutions such as JetPack or Gravity Forms.
The WordPress security team seems to have a lot of work on their hands these days, as this week they have joined efforts with Drupal to release a patch for a vulnerability in the way XML content was parsed by the PHP component in the XML-RPC implementation, which could lead to a denial-of-service condition.
According to Incapsula, over 250 million Wordpress and Drupal websites were affected until an update was pushed to the users. The large number is due to the fact that sites did not have to use XML-RPC to be vulnerable to the attack.
Other recent WordPress-related vulnerabilities refer to the MailPoet component, where a serious issue also allowed an attacker to take control of the website. The severity of the problem was very high because there was the risk of cross-site contamination, meaning that websites hosted on the same server could also be compromised, even if they did not have MailPoet installed.
A recent case of cross-site contamination was recorded for SocialBlade.com, a tracking website for YouTube statistics, which was infected through a neighboring blog that had not received updates in a long time, Jerome Segura from Malwarebytes told us at the time.
 14 DAY TRIAL //
14 DAY TRIAL //