Last year, Chinese authorities arrested several individuals believed to be involved in a cybercriminal scheme that targeted the bank accounts of e-commerce users.
Initially, police caught two of the group’s members, but after interrogating them, they learned that the gang comprised 58 individuals. 41 of them were arrested.
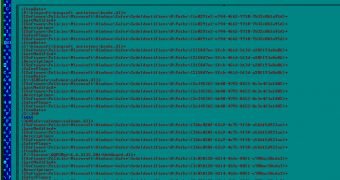
According to Kaspersky, the crooks relied on a Trojan dubbed Floating Cloud (Banker.Win32.Bancyn.a), developed in the EAZY programming language. The name stems from a Chinese saying which is translated as “God horses are always floating clouds” (everything flows away in haste like floating clouds).
The cybercriminals behind the Trojan pretended to sell various products. When a potential buyer requested details, they sent emails containing a few pictures, but also an executable which unleashed the Trojan.
Once it was executed, the malware created Group Policy files designed to prevent certain security applications from running.
Then, it identified each victim by sending the details of the infected computer back to a command and control server.
The malware injected itself into Internet Explorer and silently waited for the victim to visit a banking website. When such sites were visited, the Trojan injected malicious code into the webpage to ensure that the money transferred by the victim would be deposited in the cybercriminals’ accounts.
In some cases, payment failure messages were displayed to trick users into paying more than once.
The group was very well organized, despite the fact that its members were spread out in 32 cities. Each of them had a specific role such as programming the Trojan, obfuscating it in an effort to avoid detection, distribution, and money laundering.
They have never used their real identities and they have often changed accounts and locations to avoid being tracked down.
 14 DAY TRIAL //
14 DAY TRIAL //