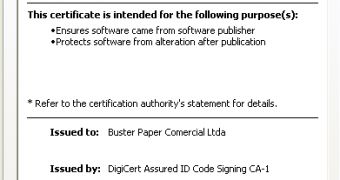
Experts from security firm Malwarebytes have identified a banking malware, Spyware.Banker.FakeSig, which uses valid digital certificates issued by DigiCert in order to increase its chances of bypassing security solutions.
The malware, which has been spotted targeting users from Brazil, relies on a certificate issued to Buster Paper Comercial Ltda, a Brazilian ghost company registered with bogus information.
The attacks start with a PDF file, which appears to represent an invoice. When it’s opened, malicious code is triggered and a connection is established with a subdomain of Egnyte, a cloud storage company.
A couple of additional payloads are downloaded from som.egnyte.com.
In addition to using valid digital certificates, the malicious files are over 10 megabytes in size. This also makes it more difficult for security solutions to neutralize the threat.
DigiCert representatives told CIO that they had immediately revoked the certificate in question. They argued that when they issued the certificate, the Buster Paper Commercial company was legally registered with the Brazil’s Ministry of Finance.
Egnyte has also addressed the issue on its end. The company has closed down the illegal account.
Jeff Hudson, the CEO of enterprise key and certificate management (EKCM) solutions provider Venafi, once again explains the importance of properly managing digital certificates.
“Organizations have deployed multi-layer defense systems designed to protect against threats from entering the network and sensitive information from leaving it, yet breaches still occur. It’s time to ask if the problem is technology or an inability to manage it correctly,” Hudson told Softpedia.
“Trust can only be maintained by knowing where vulnerabilities exist and by properly addressing those vulnerabilities, including understating where every every certificate and encryption key is on the network or cloud deployment,” Hudson added.
“Being prepared to respond to such attacks is essential, and in this case the CA revoked the certificate immediately. All organizations must have best practices put in place so that they may remediate an attack as soon as possible and minimize the damage caused. NIST and Venafi published a best practices guidance paper to help organizations in cases such as these.”
 14 DAY TRIAL //
14 DAY TRIAL //