Security firm Bitdefender has released its Threat Landscape Report for the second half of 2012.
The report highlights the fact that we’ve reached the era of state-sponsored cyberattacks, with pieces of malware such as Flame – discovered back in June – setting new complexity records.
Over the past six months cybercriminals have often relied on zero-day vulnerabilities to distribute malware. A perfect example is the JRE zero-day which was added to Metasploit two days before Oracle could address the issue.
The Internet Explorer 9 security hole discovered in September, which allowed cybercriminals to compromise computers with the notorious Poison Ivy backdoor is another example.
Both these vulnerabilities have been utilized in advanced persistent attacks.
The figures show that Trojan.AutorunInf is still the most prevalent malware, representing a total of 4.66% of detections. It’s followed by Adware.Solimba (4.41%), Exploit.CplLnk.Gen (3.54%), Win32.Worm.Downadup.Gen (3.13%) and JS:Trojan.Script.EY (3.11%).
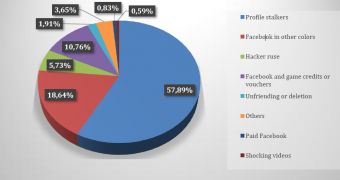
As far as social networking threats are concerned, profile stalker scams occupy the top position, followed by ones that promise Facebook in other colors, hacker ruses, voucher offers, and unfriend or deletion schemes.
When it comes to spam, pharmacy spam is the most common, amounting to 47.60%. Spam campaigns that advertise replica luxury items, casinos, and dating were also somewhat popular in the second half of 2012.
The Android threat landscape doesn’t look good. Over the past months, the number of malware infections has recorded an increase of 41%.
As expected, Trojans are still in the lead, being spotted on 74% of the infected devices.
Overall, Android.Trojan.Fake is the most common (24%), followed by Trojan.SMSSend and Trojan.GingerMaster.
The most prevalent pieces of adware are ones from the Adware.Plankton family (70%) and the Adware.Mulad family (25%).
For 2013, experts say that we should expect to see an increase in the number of Android malware samples spread through drive-by attacks and email.
The complete report is available here.
 14 DAY TRIAL //
14 DAY TRIAL //