A few days ago, Kaspersky published a report detailing the activities of a Chinese cybercriminal group dubbed Winnti. The attacks, which mainly target South East Asian organizations from the video gaming industry, started in 2009, but the campaign is still active.
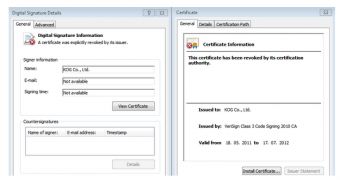
According to the security firm, the attackers are mainly focusing on stealing digital certificates and intellectual property such as source code.
To achieve its goals, the group is utilizing a penetration kit called Winnti, which allows them to gain remote access to compromised machines.
Interestingly, Kaspersky experts have identified watering hole attacks against Tibetan and Uyghur groups that rely on digital certificates stolen by the Winnti group.
Apparently, the attackers are using some of the stolen certificates to sign backdoors, which they deliver via a fairly new Flash exploit. So far, websites such as the Tibetan Homes Foundation, tibetangeeks.com, Voice of Tibet, istiqlaltv.com and maarip.org have fallen victim.
“So, what we have is an active watering hole campaign implementing a fairly new Flash exploit and abusing digital certificates that were stolen as a part of the ongoing Winnti targeted attack campaigns on game developers and publishers,” explained Kaspersky Lab Expert Kurt Baumgartner.
“The new Kaspersky Labs’ report revealing that the Winnti cybercrime organization compromised a gaming company’s system to exploit the trust every business and government depends on by stealing cryptographic keys and digital certificates should not come as a surprise,” Venafi CEO Jeff Hudson commented.
“Since Stuxnet, cybercriminals have known that compromised digital certificates – the foundation of online trust for everything from online payments, to airplanes, to your smartphone – can be used to inflict damage and steal corporate data, which is why we are seeing, more and more, the emergence of certificate-based attacks.”
“The Winnti incident is just another wake-up call for all organizations that need to secure data and protect their networks. At this point in the game, every organization must have a system in place to manage trust, and the keys and certificates that establish it, but also be ready to react when a compromise occurs,” Hudson told Softpedia.
“There simply is no reason why any organization has to suffer from a certificate-based attack or worry about a related compromise, there are solutions available today that address these problems.”
 14 DAY TRIAL //
14 DAY TRIAL //