Up until recently, Apple’s Developer Center, the Radar application to be more precise, had been plagued by a vulnerability that could have been exploited by anyone to gain access to the personal details of developers and other users.
According to 9to5mac, the security hole was discovered by developer Jesse Järvi who contacted the publication with his findings on Saturday. The existence of the issue was revealed a few hours ago, after Apple patched the flaw.
The vulnerability could have been exploited to obtain the contact information of iOS, Mac and Safari developers, Apple Retail and corporate employees, and even some key partners.
A video proof-of-concept published by Järvi shows the steps needed to exploit the bug in Apple Radar, the app used by Apple to manage bug reports submitted via the company’s bug tracker.
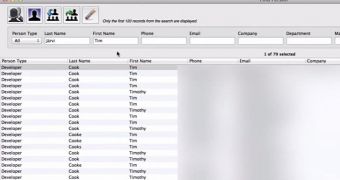
It turns out that you didn’t need any sophisticated exploits to gain access to the names, phone numbers, email addresses, company names and departments of registered developers. All that a hacker needed to do was download the Radar app, and try to log in with a random password.
Despite the fact that the app prevented the login, it still gave users access to the “Find Person” feature. Registered developers could be searched by name, phone number, email, company or department.
Apple shut down its Developer Center on Monday night while the issue was addressed. While the company hasn’t said anything about the vulnerability, iMore reports that it has removed the Radar application from its website.
Check out the proof-of-concept video for the Radar vulnerability:
 14 DAY TRIAL //
14 DAY TRIAL // 